1. Introduction
The previous nine parts introduced Monero’s privacy and confidentiality attributes in so far as senders’ identities and transaction amounts were concerned. This part focuses on privacy with respect to the recipients of funds. To that end, we introduce the stealth address system [8] to ensure that any two transactions remain unlinkable, i.e., can not be proven to be destined to the same entity.
We divide this part into two sections. The first is an overview of some of the anonymity limitations of Bitcoin. The second introduces Cryptonote’s stealth address system which when coupled with ringCT, ensures a highly anonymous and confidential environment.
2. On Bitcoin’s anonymity … or lack thereof
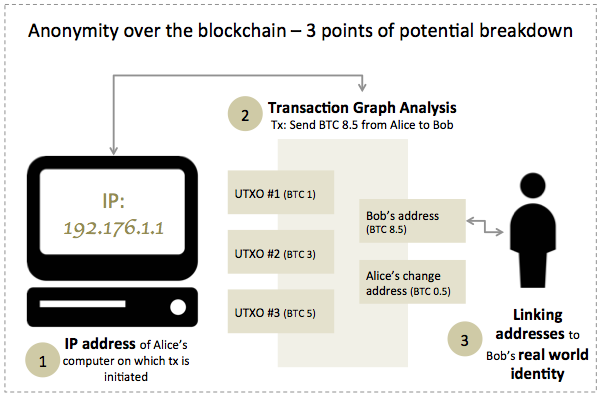
In what follows, we describe two avenues that can be used separately or jointly to conduct a deanonymization attack on Bitcoin users. The first has to do with the propagation mechanisms of Bitcoin transactions over the network, and the second with the structure of a transaction. In addition, we describe some common practices that help an attacker link a Bitcoin address to a real-world identity.
