1. Introduction
In the next 4 parts of this series, we look at various ring signature schemes and prove their security in the RO model. This part is dedicated to the analysis of a generic class of ring signature schemes introduced in [1] and inspired by [2]. We also introduce a specific instance of the generic scheme which is itself a generalization of the non-interactive Schnorr signature.
2. Herranz & Saèz generic scheme
The scheme is built on a security parameter ![]() , which by design corresponds to the length in bits of the output of the random oracle
, which by design corresponds to the length in bits of the output of the random oracle ![]() . Given a message
. Given a message ![]() and a ring
and a ring ![]() of
of ![]() members, the signing algorithm
members, the signing algorithm ![]() outputs a signature
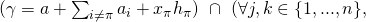
outputs a signature ![]() where:
where:
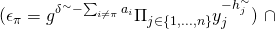
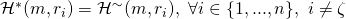
- The
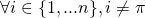
 ‘s are pairwise-different random elements chosen from a pre-defined large set. The term pairwise-different means that
‘s are pairwise-different random elements chosen from a pre-defined large set. The term pairwise-different means that  ,
, 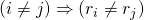 .
. 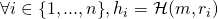 . That means that
. That means that  is the RO’s output on query
is the RO’s output on query  .
. is fully determined by
is fully determined by  , and
, and  , for all
, for all  .
.
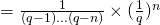
By design, we require that the probability of selecting any particular ![]() be upper-bounded by
be upper-bounded by ![]() . For example, consider the finite field
. For example, consider the finite field ![]() over a large prime
over a large prime ![]() . The probability of choosing a particular value for
. The probability of choosing a particular value for ![]() in the mutiplicative cyclic group
in the mutiplicative cyclic group ![]() is equal to
is equal to ![]() (assuming a uniform distribution over
(assuming a uniform distribution over ![]() ). Clearly, this is less than or equal to
). Clearly, this is less than or equal to ![]() .
.
3. Security analysis – Unforgeability vis-a-vis EFACM
For unforgeability proofs, we follow the 5-step approach mentioned in part 1 of this series.
Step 1: To prove that this generic scheme is secure against EFACM in the RO model, we proceed by contradiction and assume that there exists a PPT adversary ![]() such that:
such that:
(![]() non-negligible in k).
non-negligible in k).
Step 2: Next, we build a simulator ![]() such that it:
such that it:
- Does not have access to the private key of any signer.
- Has the same range as the original signing algorithm
 (i.e., they output signatures taken from the same pool of potential signatures over all possible choices of RO functions and respective random tapes
(i.e., they output signatures taken from the same pool of potential signatures over all possible choices of RO functions and respective random tapes  and
and  ).
). - Has indistinguishable probability distribution from that of
 over this range.
over this range.
![]() is specific to the particular instance of the generic scheme being used. In what follows, we build a simulator for the case of a Schnorr ring signature.
is specific to the particular instance of the generic scheme being used. In what follows, we build a simulator for the case of a Schnorr ring signature.
The Schnorr ring signature scheme is built on the finite field ![]() . Here
. Here ![]() is a large prime number and
is a large prime number and ![]() is the security parameter as described earlier. We let
is the security parameter as described earlier. We let ![]() be a generator of the multiplicative cyclic group
be a generator of the multiplicative cyclic group ![]() . We also let
. We also let ![]() be a ring of
be a ring of ![]() members where
members where ![]() has an associated key-pair given by (
has an associated key-pair given by (![]() ,
, ![]() ). The Schnorr ring signature scheme is defined as a set of 3 algorithms:
). The Schnorr ring signature scheme is defined as a set of 3 algorithms:
- The key generation algorithm
 . On input
. On input  , it produces a pair
, it produces a pair 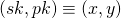 of matching secret and public keys. The algorithm is modeled as a PPT Turing machine.
of matching secret and public keys. The algorithm is modeled as a PPT Turing machine. - The ring signing algorithm
 . Suppose a user
. Suppose a user  decides to sign a message
decides to sign a message  on behalf of the ring of users
on behalf of the ring of users 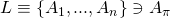 .
.  proceeds as follows:
proceeds as follows:
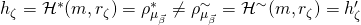
 , choose pairwise different
, choose pairwise different  ‘s at random in
‘s at random in  . Assign
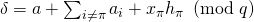
. Assign 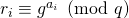 . Set
. Set 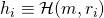 .
.- Choose a random
 . Assign
. Assign 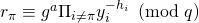 . If
. If  s.t.
s.t.  and
and  , then pick a different
, then pick a different  . Set
. Set 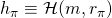 .
. - Compute
 finally outputs a signature
finally outputs a signature 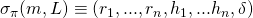 . The algorithm is modeled as a PPT Turing machine.
. The algorithm is modeled as a PPT Turing machine. - The ring verification algorithm
 . Given a ring signature
. Given a ring signature  , a message
, a message  , the set
, the set  of public keys of the ring members,
of public keys of the ring members,  verifies the validity of
verifies the validity of  by checking the following:
by checking the following:
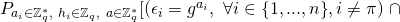
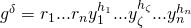
- (Verification equations
 to
to  ):
):  , for
, for 
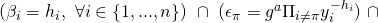
- (Verification equation
 ):
): 
 is a deterministic algorithm as opposed to probabilistic.
is a deterministic algorithm as opposed to probabilistic. - (Verification equations
Note that this scheme satisifies the correctness property. That means that any signature generated by ![]() will satisfy the verification equations with overwhelming probability. To see why, let
will satisfy the verification equations with overwhelming probability. To see why, let ![]() be a signature issued by user
be a signature issued by user ![]() on message
on message ![]() and ring
and ring ![]() of size
of size ![]() . By construction, we automatically have
. By construction, we automatically have ![]() . The first
. The first ![]() verification equations are thus met. Moreover,
verification equations are thus met. Moreover,
![]() , (by definition of
, (by definition of ![]() in
in ![]() )
)
![]()
(since by construction, ![]() for
for ![]() , and
, and ![]() ).
).
Finally, note that ![]() also mandates that
also mandates that ![]() and so
and so ![]() . Hence,
. Hence, ![]() . The last verification equation is thus met.
. The last verification equation is thus met.
We can now build a simulator specific to the Schnorr ring signature scheme:
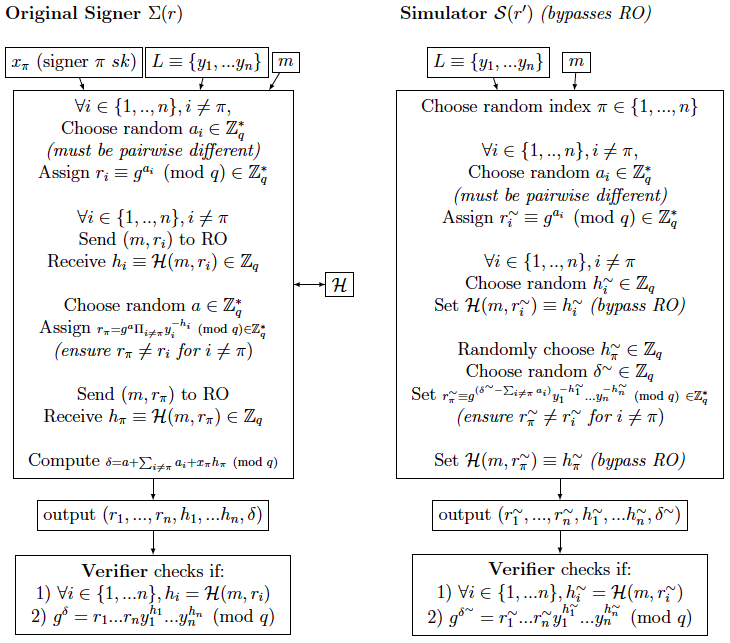
By construction, the output of ![]() will satisfy the verification equations. Moreover, it assigns a random value for each
will satisfy the verification equations. Moreover, it assigns a random value for each ![]() and bypasses the RO in doing so. Next, note the following:
and bypasses the RO in doing so. Next, note the following:
 does not use any private key.
does not use any private key. and
and  both have a range
both have a range 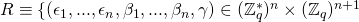 such that
such that
 and
and  have the same probability distribution over
have the same probability distribution over  . Indeed,
. Indeed, 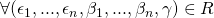 we have:
we have:
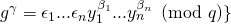
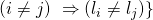
- For

![Rendered by QuickLaTeX.com P[(r_1,...,r_n,h_1,...,h_n,\delta) = (\epsilon_1,...,\epsilon_n, \beta_1,...,\beta_n, \gamma)] =](https://delfr.com/wp-content/ql-cache/quicklatex.com-7bd09541b6e950e6d531a23871d1699a_l3.png)
![Rendered by QuickLaTeX.com \epsilon_j \neq \epsilon_k)]](https://delfr.com/wp-content/ql-cache/quicklatex.com-0890368870a35da7c24e354e1ee5aca7_l3.png)
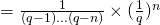
The first factor is the probability of choosing the exact
 values given by the
values given by the  ‘s
‘s  that are pairwise different. The second factor is the probability of choosing the exact
that are pairwise different. The second factor is the probability of choosing the exact  values given by the
values given by the  ‘s
‘s  .
.
- For
 :
:
![Rendered by QuickLaTeX.com P[(r^{\sim}_1,...,r^{\sim}_n,h^{\sim}_1,...,h^{\sim}_n,\delta^{\sim}) = (\epsilon_1,...,\epsilon_n, \beta_1,...,\beta_n, \gamma)] =](https://delfr.com/wp-content/ql-cache/quicklatex.com-04b8747911d3c744bfdd6da6143fb2b4_l3.png)
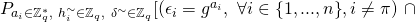
![Rendered by QuickLaTeX.com (\gamma = \delta^{\sim})\ \cap\ (\forall j,k \in \{{1,...,n\}},\ \epsilon_j \neq \epsilon_k)]](https://delfr.com/wp-content/ql-cache/quicklatex.com-061c4ea73cabe2b64f38422d24ce9ad6_l3.png)
The first factor is the probability of choosing the exact
 values given by the
values given by the  ‘s
‘s  that are pairwise different. Note that in the above,
that are pairwise different. Note that in the above,  is also an element of
is also an element of  that is different than all the other
that is different than all the other  ‘s. The second factor is the probability of choosing the exact
‘s. The second factor is the probability of choosing the exact  values given by the
values given by the  ‘s
‘s  .
.
- For
With ![]() adequately built for the Schnorr ring signature scheme, we conclude that (refer to section 6 of part 1 of this series for a justification):
adequately built for the Schnorr ring signature scheme, we conclude that (refer to section 6 of part 1 of this series for a justification):
![]() , for some
, for some ![]() non-negligible in k.
non-negligible in k.
Step 3: We now show that the probability of faulty collisions is negligible (refer to section 6 of part 1 for a description of collision types). The 2 tyes of collisions fo the generic scheme are:
 : A tuple
: A tuple  that
that  encounters — recall that
encounters — recall that  makes its own random assignment to
makes its own random assignment to  and bypasses RO — also appears in the list of queries that
and bypasses RO — also appears in the list of queries that  sends to RO. A conflict in the 2 values will happen with overwhelming probability and the execution will halt.
sends to RO. A conflict in the 2 values will happen with overwhelming probability and the execution will halt. : A tuple
: A tuple  that
that  encounters — recall that
encounters — recall that  makes its own random assignment to
makes its own random assignment to  — is the same as another tuple
— is the same as another tuple  that
that  encountered at an earlier time instance — here too,
encountered at an earlier time instance — here too,  would have made its own random assignment to
would have made its own random assignment to  . Since the 2 tuples are identical (i.e.,
. Since the 2 tuples are identical (i.e., 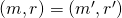 ), it must be that the 2 random assignments match (i.e.,
), it must be that the 2 random assignments match (i.e., 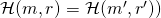 . However, the 2 values will be different with overwhelming probability and the execution will halt.
. However, the 2 values will be different with overwhelming probability and the execution will halt.
The aforementioned collisions must be avoided. In order to do so, we first calculate the probability of their occurence. We assume that during an EFACM attack, ![]() can make a maximum of
can make a maximum of ![]() queries to RO and a maximum of
queries to RO and a maximum of ![]() queries to
queries to ![]() .
. ![]() and
and ![]() are both assumed to be polynomial in the security parameter
are both assumed to be polynomial in the security parameter ![]() , since the adversary is modeled as a PPT Turing machine.
, since the adversary is modeled as a PPT Turing machine.
![]()
![]()
![]()
![]()
![]()
![]()
![]()
![]()
Note that the ![]() query (and any query in general) to
query (and any query in general) to ![]() includes an assignment of
includes an assignment of ![]() random values of the form
random values of the form ![]() for
for ![]() . This is in contrast to the Schnorr signature scheme that we encountered in part 2 of the series, and where the
. This is in contrast to the Schnorr signature scheme that we encountered in part 2 of the series, and where the ![]() query to
query to ![]() consisted of a single assignment of the form
consisted of a single assignment of the form ![]() . So we get:
. So we get:
![]()
![]()
Since ![]() and
and ![]() are polynomial in
are polynomial in ![]() , we conclude that
, we conclude that ![]() is negligible in
is negligible in ![]() .
.
Next, we compute:
![]()
![]()
![]()
Recall that the ![]() query (and any query in general) to
query (and any query in general) to ![]() includes an assignment of
includes an assignment of ![]() random values of the form
random values of the form ![]() for
for ![]() . Note that by construction of
. Note that by construction of ![]() , all the
, all the ![]() ‘s corresponding to the
‘s corresponding to the ![]() random assignments are pairwise-different and hence distinct from each-other. So in order for a certain
random assignments are pairwise-different and hence distinct from each-other. So in order for a certain ![]() value to appear twice, it must be part of 2 different queries to
value to appear twice, it must be part of 2 different queries to ![]() We can choose the 2 queries in
We can choose the 2 queries in ![]() ways. And for each one of these 2 queries, the
ways. And for each one of these 2 queries, the ![]() value can appear in any one of the
value can appear in any one of the ![]() assignments. So we get:
assignments. So we get:
![]()
![]()
And so ![]() is also negligible in
is also negligible in ![]() .
.
Putting it altogether, we find:
![]()
![]()
which is negligible in k. We can finally conclude (as per section 6 of part 1), that:
![]()
(non-negligible in ![]() )
)
Step 4: In this step, our objective is to show that if ![]() is a successful tuple that generated a first EFACM forgery, then the following quantity is non-negligible in
is a successful tuple that generated a first EFACM forgery, then the following quantity is non-negligible in ![]() :
:
![]()
![]()
Here ![]() is an appropriate index that we will define in the proof. To further simplify the notation, we let
is an appropriate index that we will define in the proof. To further simplify the notation, we let ![]() and
and ![]() for all
for all ![]() . (
. (![]() and
and ![]() denote respectively the
denote respectively the ![]() query to RO
query to RO ![]() and RO
and RO ![]() ).
).
Let’s take a closer look at ![]()
Any successful forgery must satisfy the ![]() verification equations. The first
verification equations. The first ![]() verification equations check if
verification equations check if ![]() for all
for all ![]() . And so we distinguish between 2 scenarios (w.l.o.g. we assume that all
. And so we distinguish between 2 scenarios (w.l.o.g. we assume that all ![]() -queries sent to RO are distinct from each-other since
-queries sent to RO are distinct from each-other since ![]() can keep a local copy of previous query results and avoid redundant calls):
can keep a local copy of previous query results and avoid redundant calls):
- Scenario 1:
 was successful in its forgery, and no collisions occured, and
was successful in its forgery, and no collisions occured, and  such that it never queried RO on input
such that it never queried RO on input  .
. - Scenario 2:
 was successful in its forgery, and no collisions occured, and
was successful in its forgery, and no collisions occured, and  it queried RO on input
it queried RO on input  during its execution.
during its execution.
Given a certain ![]() , the probability of scenario 1 is upperbounded by the probability that
, the probability of scenario 1 is upperbounded by the probability that ![]() picks a value for
picks a value for ![]() that matches the value of
that matches the value of ![]() . Here,
. Here, ![]() is the value that RO returns to
is the value that RO returns to ![]() (the verification algorithm) when verifying the validity of the forged signature. (It is upper-bounded because at the very least, the constraint
(the verification algorithm) when verifying the validity of the forged signature. (It is upper-bounded because at the very least, the constraint ![]() must be observed for a valid signature). And since
must be observed for a valid signature). And since ![]() can be any value in
can be any value in ![]() , we get:
, we get:
![]() (negligible in
(negligible in ![]() )
)
So we assume that a successful forgery will likely be of the Scenario 2 type. We have:
![]()
![]()
![]() (non-negligible in
(non-negligible in ![]() )
)
By definition of scenario 2, we know for a fact that ![]() , there exists an integer
, there exists an integer ![]() such that
such that ![]() is the index of the query
is the index of the query ![]() to RO. (Recall that
to RO. (Recall that ![]() represents the total number of queries that
represents the total number of queries that ![]() sends to RO). We define
sends to RO). We define ![]() to be the vector of indices
to be the vector of indices ![]() corresponding to the queries
corresponding to the queries ![]() that
that ![]() sends to RO during execution. Note that since we requested by definition that all the
sends to RO during execution. Note that since we requested by definition that all the ![]() ‘s be distinct, then so will the
‘s be distinct, then so will the ![]() ‘s. By convention, if a certain
‘s. By convention, if a certain ![]() is not queried to RO, we let its corresponding
is not queried to RO, we let its corresponding ![]() . This definition allows us to build the following sets:
. This definition allows us to build the following sets:
-
![Rendered by QuickLaTeX.com \cap\ \max_{i=1}^{n}[Ind(\omega, r', \mathcal{H})] \neq \infty\}}](https://delfr.com/wp-content/ql-cache/quicklatex.com-dd188156fbb2c1bfaef2120ed79e5d99_l3.png)
In other terms,
 is the set of tuples
is the set of tuples  that yield a successful EFACM forgery when no collisions occur, and when
that yield a successful EFACM forgery when no collisions occur, and when  queried RO on all inputs
queried RO on all inputs  (i.e., scenario 2).
(i.e., scenario 2). -
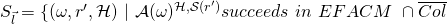
where
We let
 denote that the cardinality of
denote that the cardinality of  . We have:
. We have: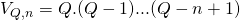
We can see that
 represents the set of tuples
represents the set of tuples  that yield a successful EFACM forgery when no collisions occur, and when
that yield a successful EFACM forgery when no collisions occur, and when  queried RO on all inputs
queried RO on all inputs 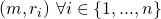 , such that the index of the input query
, such that the index of the input query  is equal to
is equal to  (i.e., the
(i.e., the  component of
component of  ).
).
Recall that, ![]() , which is non-negligible in
, which is non-negligible in ![]() .
.
Clearly, the ![]() partition
partition ![]() . So:
. So:
![]()
This implies that:
![]()
If this were not the case, then one would get the following contradiction:
![]()
So we introduce the set ![]() consisting of all vectors
consisting of all vectors ![]() that meet the
that meet the ![]() threshold, i.e.
threshold, i.e.
![]()
We claim that ![]() .
.
Proof: By definition of the sets ![]() we have:
we have:
![]()
![]()
![]()
![]()
The next step is to apply the splitting lemma to each ![]() . First note that:
. First note that:
![]()
![]()
![]()
Let ![]() . Referring to the notation used in the splitting lemma (section 7 of part 1), we let:
. Referring to the notation used in the splitting lemma (section 7 of part 1), we let:
![]() ,
, ![]() ,
, ![]() ,
, ![]() , and
, and ![]()
![]() is defined as the space of tuples of all random tapes
is defined as the space of tuples of all random tapes ![]() , all random tapes
, all random tapes ![]() , and all possibe RO answers to the first
, and all possibe RO answers to the first ![]() queries sent by
queries sent by ![]() .
. ![]() is defined as the space of all possible RO answers to the last
is defined as the space of all possible RO answers to the last ![]() queries sent by
queries sent by ![]() . (Recall that
. (Recall that ![]() . The splitting lemma guarantees the existence of a subset
. The splitting lemma guarantees the existence of a subset ![]() of tuples
of tuples ![]() such that:
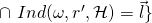
such that:
![Rendered by QuickLaTeX.com P_{\omega,r',\mathcal{H}}[(\omega, r', \mathcal{H}) \in \Omega_{\vec{l}}] \geq \frac{\nu(k)}{4V_{Q,n}}](https://delfr.com/wp-content/ql-cache/quicklatex.com-395ce19a833d9891b31e9fe7316cd428_l3.png)
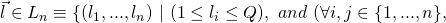
![Rendered by QuickLaTeX.com \forall [(\omega^{\sim}, r'^{\sim}, \mathcal{H}^{\sim}) \equiv (\omega^{\sim}, r'^{\sim}, \rho_1^{\sim}, ..., \rho_{{\mu_{\vec{l}}}\ -1}^{\sim}, \rho_{\mu_{\vec{l}}}^{\sim} ... \rho_{Q}^{\sim}]) \in \Omega_{\vec{l}}](https://delfr.com/wp-content/ql-cache/quicklatex.com-78cab1206dd54a556a09652ef67b4cea_l3.png) , we have
, we have
![Rendered by QuickLaTeX.com P_\mathcal{H}[(\omega^{\sim}, r'^{\sim}, \rho_1^{\sim}, ..., \rho_{{\mu_{\vec{l}}}\ -1}^{\sim}, \rho_{\mu_{\vec{l}}} ... \rho_{Q}) \in S_{\vec{l}}\ |\ (\omega^{\sim}, r'^{\sim}, \mathcal{H}^{\sim}) \in \Omega_{\vec{l}}]](https://delfr.com/wp-content/ql-cache/quicklatex.com-73d636b1ed4f57530da10138680f133c_l3.png)
 , and so:
, and so: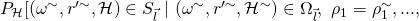
![Rendered by QuickLaTeX.com \rho_{{\mu_{\vec{l}}}\ -1} = \rho_{{\mu_{\vec{l}}}\ -1}^{\sim})]\ \geq \frac{\nu(k)}{4V_{Q,n}}](https://delfr.com/wp-content/ql-cache/quicklatex.com-fbb5180f775f714f3e26186b5e956162_l3.png)
![Rendered by QuickLaTeX.com P[(\omega, r', \mathcal{H}) \in \Omega_{\vec{l}}\ |\ (\omega, r', \mathcal{H}) \in S_{\vec{l}}] \geq (\frac{\nu(k)}{4V_{Q,n}}) / (\frac{\nu(k)}{2V_{Q,n}}) = \frac{1}{2}](https://delfr.com/wp-content/ql-cache/quicklatex.com-ba15c669ffccca6f586c34b34d717233_l3.png)
We would like to compute the probability of finding a ![]() successful tuple
successful tuple ![]() given that
given that ![]() was a successful
was a successful ![]() tuple and such that
tuple and such that ![]() .
.
That means finding the following probability:
![]()
From the splitting lemma results, we have a (non-negligible in ![]() ) lower-bound on
) lower-bound on
![]()
Note however, that ![]() and
and ![]() are generally distinct sets. And so we cannot conclude that
are generally distinct sets. And so we cannot conclude that
![]()
![]()
and therefore we cannot conclude that the following is non-negligible in ![]()
![]()
In order to show that the above quantity is non-negligible in ![]() , we proceed differently. Suppose we can show that the following probability is non-negligible in
, we proceed differently. Suppose we can show that the following probability is non-negligible in ![]() :
:
![]()
This would imply that with non-negligible probability, we can find a tuple that belongs to ![]() (and hence corresponds to a successful forgery) and at the same time belongs to
(and hence corresponds to a successful forgery) and at the same time belongs to ![]() . We can then invoke the splitting lemma result just mentioned, to find a second tuple coresponding to a second forgery and that has the desired properties.
. We can then invoke the splitting lemma result just mentioned, to find a second tuple coresponding to a second forgery and that has the desired properties.
To prove the above, we proceed as follows:
![]()
![]()
![]() , since the
, since the ![]() ‘s are disjoint
‘s are disjoint
![]()
![]()
![]()
![]() , (
, (![]() result of splitting lemma above)
result of splitting lemma above)
![]() (by the claim proven earlier)
(by the claim proven earlier) ![]() .
.
And so we conclude that:
![]()
![]()
![]()
![]()
![]() , which is non-negligible in
, which is non-negligible in ![]() .
.
So let ![]() be such an index and
be such an index and ![]() such a tuple. From the result above, we know that finding such a
such a tuple. From the result above, we know that finding such a ![]() can be done with non-negligible probability. And since
can be done with non-negligible probability. And since ![]() , we must have
, we must have ![]() . We can then invoke the
. We can then invoke the ![]() consequence of the splitting lemma, and write:
consequence of the splitting lemma, and write:
![]()
![]()
![]()
We still have one last constraint to impose and that is that ![]() . We show that the following quantity is non-negligible:
. We show that the following quantity is non-negligible:
![]()
![]()
To prove this, note that if ![]() and
and ![]() are independent events, then we can write:
are independent events, then we can write:
![]()
![]()
And so we get ![]() . This results allows us to write:
. This results allows us to write:
![]()
![]()
![]()
![]()
![]()
![]() , (because we chose
, (because we chose ![]()
![]() (non-negligible in
(non-negligible in ![]() )
)
Step 5: The final step uses the 2 forgeries obtained earlier to solve an instance of the Discrete Logarithm (DL) problem. Here is a recap of Step 4 results:
- With non-negligible probability of at least
 we get a successful tuple
we get a successful tuple  , s.t.
, s.t. 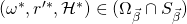 for some vector of indices
for some vector of indices  . So by running
. So by running  a number of times polynomial in
a number of times polynomial in  , we can confidently find such a tuple.
, we can confidently find such a tuple. - Once we find such a tuple, we’ve also shown that with non-negligible probability of at least
 , we can find another successful tuple
, we can find another successful tuple  such that
such that 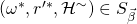 and
and 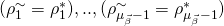 , but
, but  .
.
Without loss of generality, let
![]() correspond to
correspond to ![]() , and
, and
![]() correspond to
correspond to ![]() .
.
Recall that ![]() is the vector
is the vector ![]() where
where ![]() denotes the index of query
denotes the index of query ![]() that
that ![]() sends to the RO. Since the 2 experiments corresponding to the 2 successful tuples have the same random tapes
sends to the RO. Since the 2 experiments corresponding to the 2 successful tuples have the same random tapes ![]() and
and ![]() , and since the 2 corresponding ROs
, and since the 2 corresponding ROs ![]() and
and ![]() behave the same way on the first
behave the same way on the first ![]() queries (recall that
queries (recall that ![]() , we can be confident that:
, we can be confident that:
- The first
 queries sent to the 2 ROs are identical. In particular,
queries sent to the 2 ROs are identical. In particular, 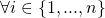 we have
we have 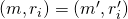 .
. - The first (
 ) replies of the 2 oracles
) replies of the 2 oracles  and
and  are the same. Suppose w.l.o.g. that
are the same. Suppose w.l.o.g. that  , (where
, (where  ), corresponds to the last query of this type that is sent to the ROs.
), corresponds to the last query of this type that is sent to the ROs.  is actually the
is actually the  query sent to RO (by definition of
query sent to RO (by definition of  ). We then have
). We then have
So we have 2 successful forgeries ![]() and
and ![]() , with
, with ![]() . Since both are valid signatures, they must satisfy the verification equations. For the particular case of a Schnorr ring signature, they must satisfy the following 2 equations (1 equation per signature):
. Since both are valid signatures, they must satisfy the verification equations. For the particular case of a Schnorr ring signature, they must satisfy the following 2 equations (1 equation per signature):
 , where
, where  is the set of public keys of the
is the set of public keys of the  ring members associated with the signature.
ring members associated with the signature.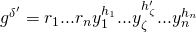 , where
, where  is the set of public keys of the
is the set of public keys of the  ring members associated with the signature.
ring members associated with the signature.
Writing ![]() (
(![]() is the secret key corresponding to
is the secret key corresponding to ![]() ), we get:
), we get:
![]()
Since, ![]() , we can solve for
, we can solve for ![]() (the DL of
(the DL of ![]() ) in polynomial time. This contradicts the intractability of DL on multiplicative cyclic groups and we conclude that our signature scheme (in this case the Schnorr ring signature scheme) is secure against EFACM in the RO model.
) in polynomial time. This contradicts the intractability of DL on multiplicative cyclic groups and we conclude that our signature scheme (in this case the Schnorr ring signature scheme) is secure against EFACM in the RO model.
4. Security analysis – Anonymity
In this section, we show that our generic scheme satisfies the anonymity definition #1 introduced in part 3 of this series. Recall that roughly speaking, this definition mandates that the probability of guessing the real signer be ![]() (in an
(in an ![]() -ring setting). This probability is independent of any knowledge about any member’s private key. In other terms, even if a signer is coerced or subpoenaed to release her private key, nothing can be done to prove that she is the real signer (with probability better than random guessing).
-ring setting). This probability is independent of any knowledge about any member’s private key. In other terms, even if a signer is coerced or subpoenaed to release her private key, nothing can be done to prove that she is the real signer (with probability better than random guessing).
To prove anonymity in our case, we show that any signature could have been created with equal probability by any of the ![]() members of the ring. We show that releasing information about the secret key of any ring member does not modify this probability. That automatically implies that even when a subset of private keys gets compromised, there is still an equiprobable likelihood that the signature was created by any member.
members of the ring. We show that releasing information about the secret key of any ring member does not modify this probability. That automatically implies that even when a subset of private keys gets compromised, there is still an equiprobable likelihood that the signature was created by any member.
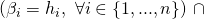
Proof: Let ![]() be a valid signature on message
be a valid signature on message ![]() and ring
and ring ![]() . That means that all
. That means that all ![]() verification equations are satisfied. Let
verification equations are satisfied. Let ![]() be any member of the ring (with compromised or non-compromised secret key
be any member of the ring (with compromised or non-compromised secret key ![]() The probability that
The probability that ![]() was issued by
was issued by ![]() is given by:
is given by:
![]()
![]()
![]()
![]()
Note that once the ![]() ‘s are calculated, the
‘s are calculated, the ![]() ‘s will be automatically determined since we are using a specific hash function. Clearly, the above probability does not depend on any specific information about member
‘s will be automatically determined since we are using a specific hash function. Clearly, the above probability does not depend on any specific information about member ![]() . It is the same for all ring members.
. It is the same for all ring members.
References
[1] J. Herranz and G. Saez. Forking lemmas in the ring signatures’ scenario. Proceedings of INDOCRYPT’03, Lecture Notes in Computer Science(2904):266{279, 2003.
[2] D. Pointcheval and J. Stern. Security arguments for digital signatures and blind signatures. Journal of Cryptology, 2000.
Tags: anonymity, Crypto, Privacy, ring signature, Schnorr

No comments
Comments feed for this article
Trackback link: https://delfr.com/herranz-saez-ring-signature-moneros-building-blocks-part-4-10/trackback/