1. Introduction and motivation
The sempiternel question of how to gain and maintain power has haunted the minds of humanity’s brightest and darkest since the dawn of civilization. Be it physical (e.g., military) or economical (e.g., wealth), power’s very existence relied in part on access to information. Asymmetric information that is. Numerous are history’s examples that demonstrate how entities that knew what others didn’t and that were able to act on it, benefited from an unfair advantage. The quest for sustainable power motivates the protection of one’s proprietary information and the attempt at breaching that of the others.
Although significant in its own right, the pursuit of power is not the only motivator to conceal information. Privacy, in so far as the individual’s well-being is concerned, is another. In that respect, two areas stand out. The first is concerned with the unique nature of a human persona. As a matter of observation, and at the risk of irritating adherents of monism, the attributes of a human personality are so varied. Each attribute exists on a wide spectrum, making it unlikely that any two individuals have the same profile so to speak. The privacy spectrum is no exception, and while some live their lives as an open book, others might not even be comfortable sharing their half title page. The second area is concerned with the safety of a certain subset of individuals, e.g., whistle-blowers. They may hold sensitive information destined to be shared with a specific party. Should this information fall in the wrong hands, it could jeopardize the safety of the source.
It is therefore reasonable to assume that not every piece of information is meant to be common knowledge. One could certainly debate the merits of such a claim and in the process, revisit the very foundation of power, privacy and safety. The fact remains however, that information can be a source of influence, discomfort, and danger. One way of protecting specific content and limiting its access to intended parties only, is through the use of encryption and decryption algorithms.
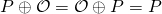
Symmetric-key vs. public key cryptography: Encryption can be thought of as a map that takes a relevant piece of data known as a message, and outputs an altered version of it. The map can be either one of two types: 1) PT-invertible, or 2) One-way.
- We say that a function is PT-invertible if one can find a polynomial-time algorithm to compute its inverse. In order for a sender to encrypt a message, he must be able to compute the map. On the other end, in order for a recipient to decrypt the message, she must be able to compute the inverse map. If a map is PT- invertible, information used to build it is sufficient to build its inverse. As a result, senders and recipients alike can use the same information to encrypt and to decrypt messages in a process known as symmetric-key cryptography. The symmetric information shared between the sender and the recipient is known as the secret key.
As an example, consider a message space consisting of the case-agnostic latin alphabet of 26 letters. We represent each letter by its numerical equivalent (e.g., letter “a” or “A” represented by 1), and apply the following affine map:
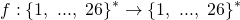
where the
 superscript denotes a string of arbitrary length, and
superscript denotes a string of arbitrary length, and  are pre-defined elements in
are pre-defined elements in  such that
such that  is relatively prime to 26.
is relatively prime to 26.For instance, let
 and
and  The word “chaos” has a representation given by (3, 8, 1, 15, 19). When fed to the map, one obtains an output given by
The word “chaos” has a representation given by (3, 8, 1, 15, 19). When fed to the map, one obtains an output given by 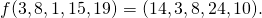 This corresponds to “nchxj”.
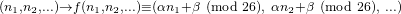
This corresponds to “nchxj”.The inverse map can be written as follows:
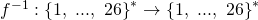

where
 is the inverse of
is the inverse of  in modulo 26 arithmetic (i.e.,
in modulo 26 arithmetic (i.e.,  Since,
Since,  and 26 are relatively prime, one can use the extended euclidean algorithm outlined in the Groups and Finite Fields post to calculate
and 26 are relatively prime, one can use the extended euclidean algorithm outlined in the Groups and Finite Fields post to calculate  in polynomial time. Consequently,
in polynomial time. Consequently,  is a PT-invertible map. All that is required to build it and its inverse is the pair
is a PT-invertible map. All that is required to build it and its inverse is the pair  This pair constitutes the symmetric key shared between the sender and the recipient.
This pair constitutes the symmetric key shared between the sender and the recipient.Symmetric-key cryptography is known to be efficient, with the possibility of encrypting and decrypting large amounts of data relatively fast. Its weakness however, lies in the fact that the secret key must be shared between two (or more) parties over a secure channel. Enforcing perfect security and eliminating the risk of leakage over a digital communication channel is a challenging endeavour. Moreover, if such a secure medium of communication could be constructed, it would be legitimate to question the usefulness of sharing a secret key in the first place as opposed to using the secure channel to directly send and receive the actual messages.
- One-way or trapdoor functions have no known polynomial-time algorithm to compute their inverses in the absence of a specific piece of information referred to as the trapdoor. In other words, knowledge of the building blocks of a map is not sufficient to compute its inverse. In order to do so (and as a result decrypt a message), a recipient must have access to the trapdoor.
Algorithms where the information needed to encrypt is different than that needed to decrypt, form the basis of asymmetric cryptography. The nomenclature is a reflection of the informational asymmetry between encryption and decryption. More specifically, each recipient is associated with a key pair consisting of a unique private key only known to her, and a related public key that can be shared with anyone. Anyone can use the public key of a recipient to encrypt a message. Decryption however, requires knowledge of the private key which is only known to the recipient. In light of the above, a crucial criterion in the design of key pairs is that no entity should be able to derive the private key from the public one. The dual-key architecture is the reason why asymmetric cryptography is also known as public-key cryptography.
As an example we consider the RSA encrytion scheme. RSA generates the public and private keys of a user as follows:
-
Select two very large primes
 and
and  such that
such that 
-
Let
 One can observe that given
One can observe that given  and
and  it is easy to compute
it is easy to compute  . However, given
. However, given  , it is extremely challenging to find
, it is extremely challenging to find  and
and  . This is known as the factoring problem, thought to be intractable on the group
. This is known as the factoring problem, thought to be intractable on the group  .
. -
Find
 ‘s totient value
‘s totient value  Euler’s totient function returns the number of integers less than or equal to
Euler’s totient function returns the number of integers less than or equal to  that are relatively prime to
that are relatively prime to  . If
. If  is prime, then
is prime, then  . In addition, for any two coprime numbers
. In addition, for any two coprime numbers  and
and  ,
,  . Consequently,
. Consequently,
- Choose
 such that
such that  and such that
and such that  . We let
. We let  be the public key of the user.
be the public key of the user. - Choose
 such that
such that 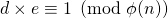 . That means that
. That means that 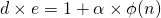 for some integer
for some integer  . We observe that even if
. We observe that even if  were known, it is computationally hard to calculate
were known, it is computationally hard to calculate  because this requires computing
because this requires computing  and
and  which in turn, requires solving the prime factorization problem. This in turn, makes it challenging to calculate
which in turn, requires solving the prime factorization problem. This in turn, makes it challenging to calculate  We let
We let  be the private key of the user. The previous observation shows that it is unlikely for anyone to derive the private key
be the private key of the user. The previous observation shows that it is unlikely for anyone to derive the private key  from the public key
from the public key  alone.
alone.
To encrypt a message destined to Bob, Alice first transforms it into an integer
 by using a common-knowledge pre-defined mapping. We require that
by using a common-knowledge pre-defined mapping. We require that  and
and  be coprime. Subsequently, Alice computes the encrypted value
be coprime. Subsequently, Alice computes the encrypted value 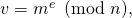 where
where  is Bob’s public key. In order to decrypt the message, Bob uses his private key
is Bob’s public key. In order to decrypt the message, Bob uses his private key  to compute
to compute  To see why this works, note the following equalities:
To see why this works, note the following equalities: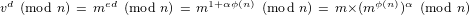
We can invoke Euler’s theorem that states that if
 and
and  are relatively prime, then
are relatively prime, then  (proof ommitted). We conclude that
(proof ommitted). We conclude that
Note that when the public key
 is known, it is straightforward to compute
is known, it is straightforward to compute  However, calculating its inverse (i.e., finding the value of
However, calculating its inverse (i.e., finding the value of  when
when  and
and  are known) is thought to be hard. On the other hand, knowledge of the private key
are known) is thought to be hard. On the other hand, knowledge of the private key  allows a quick retrieval of
allows a quick retrieval of  as we saw above.
as we saw above. -
A downside of public key cryptography is that it is not nearly as efficient as its symmetric counterpart, especially as the message size increases. However, symmetric-key cryptography depends on the existence of a secure channel which is challenging to build. The upside of asymmetric cryptography is that it bypasses the need for a secure channel altogether. It turns out that one can leverage the advantage of each type of cryptography to create a hybrid system that is both secure and efficient. This is accomplished through the use of a key-exchange protocol known as a Diffie-Hellman exchange.
The idea is to simply apply public-key cryptography to communicate a shared secret, which can then be used in a symmetric-key setting to encrypt and decrypt larger messages. Since the secret-key is relatively small (from a data standpoint), it can be encrypted rather efficiently using a public-key setting and then shared with a recipient on an untrusted channel. Larger message blocks can subsequently be effectively encoded and decoded using the secret key. More formally, an example of this setting can be described as follows:
- Consider the multiplicative cyclic group
 of the finite field
of the finite field  of large prime order
of large prime order  (The reader can consult the Group and Finite Fields post for more details). Let
(The reader can consult the Group and Finite Fields post for more details). Let  be one of its generators.
be one of its generators. - Alice and Bob chose their individual secret keys
 from
from 
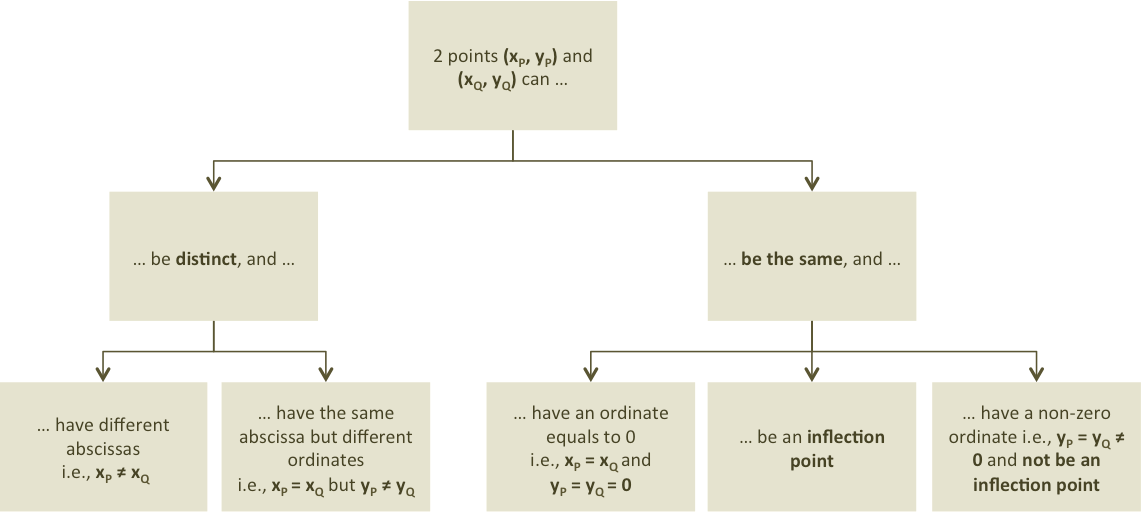
- They compute their respective public keys
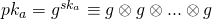 (
( times)
times)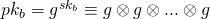 (
( times)
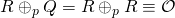
times) - Bob uses Alice’s public key to compute
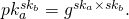 Similarly, Alice uses Bob’s public key to compute
Similarly, Alice uses Bob’s public key to compute 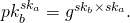
- The two previously calculated values are equal and known only to Alice and Bob. This is because its calculation requires knowledge of at least one of the two secret keys. It can then be used as a shared secret as part of a symmetric-key algorithm.
As noted earlier, the most important design criterion is to ensure that the secret key cannot be derived from the public key. In our setting, this means that when given ![]() and
and ![]() no one should be able to calculate in polynomial time the value of
no one should be able to calculate in polynomial time the value of ![]() This is known as the discrete logarithm (DL) problem and we will revisit it. On the multiplicative group of a finite field of large prime order, the DL problem is thought to be hard.
This is known as the discrete logarithm (DL) problem and we will revisit it. On the multiplicative group of a finite field of large prime order, the DL problem is thought to be hard.
Digital signatures: Encryption schemes help protect the content. However, they provide no proof that a certain sender was the actual author. This is true especially in the context of public-key cryptography where encryption keys are made public, allowing any party to claim that it was the actual sender. This problem can have drastic consequences when dealing with cryptocurrencies. Indeed, a cryptocurrency transaction consists of a message whose content allows a transfer of spending control from one owner to another. In Bitcoin for example, all valid transactions are publicly registered on the blockchain, and their content is purposefully not encrypted in order to enforce transparency and allow nodes to validate or reject them. However, the message in this case must be accompanied by a proof that the sender is actually the initiator of the transaction. Otherwise, anyone could initate a transaction on behalf of someone else without their consent, potentially causing financial mayhem.
The authentication process is done through the use of a mathematical construct known as a digital signature. In the context of cryptocurrencies, we care about digital signature and less so about encryption. The most important attribute of a digital signature is that of unforgeability. This can be defined in a variety of ways, but for all practical matters we mean resilience against existential forgery in the adaptive chosen-message attack. More details about digital signatures and the definitions of forgery can be found in the post entitled Digital Signature and Other Prerequisites. Generally speaking, digital signatures use the same public-key cryptography infrastructure described earlier for encryption and decryption. The sender signs with her private key in order to authenticate the message. Anyone on the network can then verify that she was the actual sender by running a verification algorithm that relies on the sender’s public key. Various examples of digital signatures including Schnorr, RSA, generic Pointcheval & Stern models, as well as a number of more elaborate ring signature schemes can be found in previous posts.
The discrete logarithm problem: A necessary condition to avoid forgery is that no one should be able to derive the private key from the public one. Here too, we realize the cruciality of one-way constructs. An important example of such a construct is the one associated with the DL poblem encountered earlier. The hardness of the DL problem on some well-defined groups underlies the security of various digital signature schemes, including those adopted in cryptocurrencies. Formally, we define the DL problem as follows:
- Let
 be a given group and
be a given group and  an element of
an element of 
- Given an element
 (i.e., the subgroup generated by
(i.e., the subgroup generated by  ), find an integer
), find an integer  such that
such that 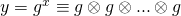 (
( times).
times).
The smallest ![]() that satisfies the above equation is known as the logarithm of
that satisfies the above equation is known as the logarithm of ![]() in base
in base ![]() and we write
and we write ![]()
The difficulty associated with calculating ![]() knowing
knowing ![]() and
and ![]() depends on the underlying group
depends on the underlying group ![]() On some groups, the problem is easy to solve (i.e., we know of polynomial-time algorithms that can solve it). On others, it is harder. Moreover, there exists different levels of difficulty, the highest being exponential (i.e., the only known algorithm(s) to solve the problem are exponential in time). In the context of public-key cryptography, it is always desirable to operate on groups where the hardness of the DL problem is exponential.
On some groups, the problem is easy to solve (i.e., we know of polynomial-time algorithms that can solve it). On others, it is harder. Moreover, there exists different levels of difficulty, the highest being exponential (i.e., the only known algorithm(s) to solve the problem are exponential in time). In the context of public-key cryptography, it is always desirable to operate on groups where the hardness of the DL problem is exponential.
An example of a group on which the DL problem is easy to solve is ![]() (i.e., the group of integers modulo
(i.e., the group of integers modulo ![]() introduced in the Group and Finite Fields post). To see why, first note that this group is cyclic and that the equivalence class
introduced in the Group and Finite Fields post). To see why, first note that this group is cyclic and that the equivalence class ![]() is a generator. Given
is a generator. Given ![]() the DL problem consists in finding
the DL problem consists in finding ![]() such that
such that
![]() (
(![]() times)
times)
By the definition of ![]() this is equivalent to finding
this is equivalent to finding ![]() such that
such that ![]() i.e.,
i.e., ![]() such that
such that ![]() Consequently, one can compute
Consequently, one can compute ![]() efficiently using the Euclidean algorithm.
efficiently using the Euclidean algorithm.
An example of a group on which the DL problem is believed to be hard is the multiplicative group ![]() of the finite-field
of the finite-field ![]() of large prime order
of large prime order ![]() This group is cyclic and was introduced in the Group and Finite Fields post. The time required by the best-known algorithm to solve DL on it is
This group is cyclic and was introduced in the Group and Finite Fields post. The time required by the best-known algorithm to solve DL on it is ![]() [10]. The running time is sub-exponential i.e., executes faster than an exponential algorithm but is less efficient than a polynomial one.
[10]. The running time is sub-exponential i.e., executes faster than an exponential algorithm but is less efficient than a polynomial one.
Despite the hardness of DL on the multiplicative cyclic subgroup of a large finite field, it remains more desirable to operate on groups where the DL is thought to be exponentially hard. An example of such a group is the one associated with elliptic curves over finite fields. The elliptic curve discrete logarithm problem (ECDLP) over ![]() is thought to be exponentially hard, with the best performing algorithm requiring time
is thought to be exponentially hard, with the best performing algorithm requiring time ![]() [10].
[10].
By way of comparison, ECDLP on a finite field of order ![]() has an equivalent difficulty to a DL problem on the multiplicative cyclic subgroup of
has an equivalent difficulty to a DL problem on the multiplicative cyclic subgroup of ![]() One implication is that cryptographic primitives based on ECDLP require significantly smaller keys. This explains why the digital signature schemes used in various cryptocurrencies (e.g., Bitcoin’s ECDSA, Monero’s MLSAG) rely on elliptic curve groups.
One implication is that cryptographic primitives based on ECDLP require significantly smaller keys. This explains why the digital signature schemes used in various cryptocurrencies (e.g., Bitcoin’s ECDSA, Monero’s MLSAG) rely on elliptic curve groups.
With this motivation behind us, we are now in a position to introduce the concept of an elliptic curve. Its theory is very rich and sits at the intersection of different branches of mathematics including analysis, geometry, and algebra. Our objective is to build a group structure based on the geometry of elliptic curves. The new group is referred to as an elliptic curve group and forms the public-key infrastructure of a number of cryptocurrencies in use today. We highlight that this introduction is limited to the minimum that we think is needed to appreciate the subject. It is by no means a comprehensive treatise. Readers interested in a detailed treatment of elliptic curve theory can consult e.g., [10]
In what follows, we first introduce an analytic view of elliptic curves over arbitrary fields. We describe the general Weierstrass form and derive a more simplified version as long as some constraints are observed. We then look at the geometry of elliptic curves over real numbers, and build a group structure after augmenting the curve with a point at infinity. The group’s binary operation, also referred to as point addition, is described geometrically and analytically. Later, we introduce the elliptic curve group over finite fields and finally, we describe the two elliptic curves used in Bitcoin and in Monero.
2. Elliptic curves: An analytic description
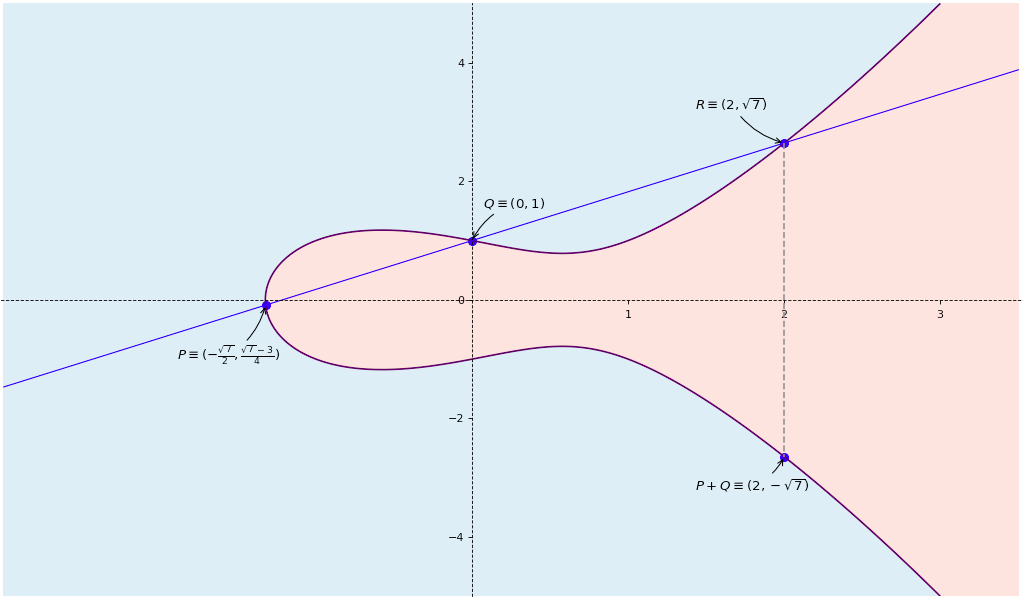
One way of defining an elliptic curve is as a set of points satisfying the Weierstrass general equation and given by:
![]()
The coefficients ![]() are chosen from a field
are chosen from a field ![]() and we say that
and we say that ![]() is defined over
is defined over ![]() Note that
Note that ![]() is purposefully left out for reasons that we keep out of scope for now.
is purposefully left out for reasons that we keep out of scope for now. ![]() could be for instance the field of real numbers
could be for instance the field of real numbers ![]() or any finite field. Recall that in the Groups and Finite Fields post we mentioned that any finite field is either of prime order
or any finite field. Recall that in the Groups and Finite Fields post we mentioned that any finite field is either of prime order ![]() or is an extension
or is an extension ![]() of a field of prime order
of a field of prime order ![]() where
where ![]() can be any positive integer. We refer to
can be any positive integer. We refer to ![]() as the characteristic of the finite field
as the characteristic of the finite field ![]() and write
and write ![]() We derive below a simplified version of the Weierstrass equation applicable only if we exclude fields of characteristics 2 and 3.
We derive below a simplified version of the Weierstrass equation applicable only if we exclude fields of characteristics 2 and 3.
Let’s first look at the left-hand side of the equation. It is tempting to complete the quadratic in ![]() We can always find
We can always find ![]() such that
such that
![]()
We could subsequently make a change of variables by substituting ![]() with
with ![]() Since
Since ![]() does not depend on
does not depend on ![]() we would have eliminated all terms that contain
we would have eliminated all terms that contain ![]() as a factor. The aforementioned equation in
as a factor. The aforementioned equation in ![]() can equivalently be written as
can equivalently be written as
![]()
One would then be tempted to conclude that ![]() except that division by 2 is not always permissible on an arbitrary field
except that division by 2 is not always permissible on an arbitrary field ![]() If
If ![]() then
then ![]() will not admit a multiplicative inverse on
will not admit a multiplicative inverse on ![]() However, division by 2 is possible on all other fields. In what follows, we always assume that
However, division by 2 is possible on all other fields. In what follows, we always assume that ![]() Consequently, we can compute
Consequently, we can compute ![]() and perform the change of variable. The Weierstrass equation becomes:
and perform the change of variable. The Weierstrass equation becomes:
![]()
![]()
![]()
Letting ![]() and
and ![]() the elliptic curve equation becomes:
the elliptic curve equation becomes:
![]()
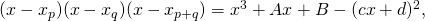
The next step consists in simplifying the right hand-side of this equation. It turns out that any cubic equation can be transformed into an equivalent one with the quadratic term eliminated. We do so by substituting variable ![]() with a variable of the form
with a variable of the form ![]() The value of
The value of ![]() is derived by first performing the substitution and then eliminating the coefficient of the quadratic term as follows:
is derived by first performing the substitution and then eliminating the coefficient of the quadratic term as follows:
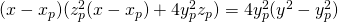
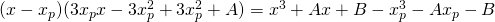
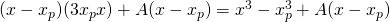
![]()
![]()
![]()
We require that the coefficient of ![]() be equal to 0. This imposes a constraint on
be equal to 0. This imposes a constraint on ![]() ‘s value which must satisfy:
‘s value which must satisfy:
![]()
If ![]() we can always find a multiplicative inverse of
we can always find a multiplicative inverse of ![]() in
in ![]() and as a result, solve for
and as a result, solve for ![]() The elliptic curve equation becomes:
The elliptic curve equation becomes:
![]()
We can relabel the ![]() variables as
variables as ![]() and let
and let ![]() and
and ![]() We then obtain the simplified Weierstrass equation of an elliptic curve over a field
We then obtain the simplified Weierstrass equation of an elliptic curve over a field ![]() such that
such that ![]()
![]()
In the following section we construct a group structure over elliptic curves. The tangent to the curve at a given point will play an essential role in this construction. As a result, elliptic curves that have singularities (i.e., points where the curve is not differentiable) are not desired and will be excluded. Examples of singularities on a curve include cusps and self intersections. Analytically, a necessary and sufficient condition for a point ![]() on a curve
on a curve ![]() to be singular is for the partial derivatives at
to be singular is for the partial derivatives at ![]() to be equal to 0. For the elliptic curve equation we get:
to be equal to 0. For the elliptic curve equation we get:
The last equation implies that ![]() If we substitute
If we substitute ![]() in the first and second equations, we conclude that
in the first and second equations, we conclude that
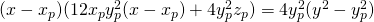
![]() is singular
is singular ![]() and
and ![]()
Consequently, ![]() must be a cubic root of
must be a cubic root of ![]() as well as of its derivative
as well as of its derivative ![]() This means that
This means that ![]() is a double root of
is a double root of ![]() If we let
If we let ![]() denote the third root, we get the following factorization:
denote the third root, we get the following factorization:
![]()
![]()
By comparing coefficients, we find that ![]() ,
, ![]() and
and ![]() This in turn implies that the discriminant
This in turn implies that the discriminant ![]() To summarize, we showed that given an elliptic curve
To summarize, we showed that given an elliptic curve ![]() over a field
over a field ![]() such that
such that ![]() we have:
we have:
![]() is singular
is singular ![]()
The contrapositive statement allows us to derive a sufficient condition for ![]() to be non-singular. Specifically, if
to be non-singular. Specifically, if ![]() for all
for all ![]() then
then ![]() is non-singular. Going forward, we only consider non-singular elliptic curves defined over fields of characteristic other than 2 or 3:
is non-singular. Going forward, we only consider non-singular elliptic curves defined over fields of characteristic other than 2 or 3:
![]()
3. Elliptic curve groups: A geometric approach
In what follows, we endeavour to build the elliptic curve group over finite fields. To do so, we first consider elliptic curves over ![]() and study their geometry in order to devise a natural abelian group structure. Technically, the construction is performed in the projective plane as opposed to the euclidean plane. However, we attempt to motivate and justify the build-up without delving into the technicalities of projective geometry. Finally, we adapt the binary operation of the group to the case of a finite field.
and study their geometry in order to devise a natural abelian group structure. Technically, the construction is performed in the projective plane as opposed to the euclidean plane. However, we attempt to motivate and justify the build-up without delving into the technicalities of projective geometry. Finally, we adapt the binary operation of the group to the case of a finite field.
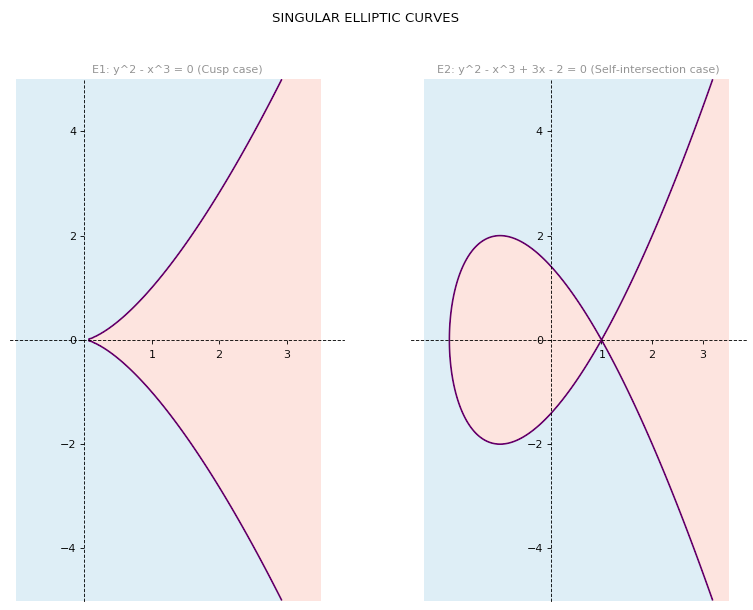
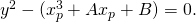
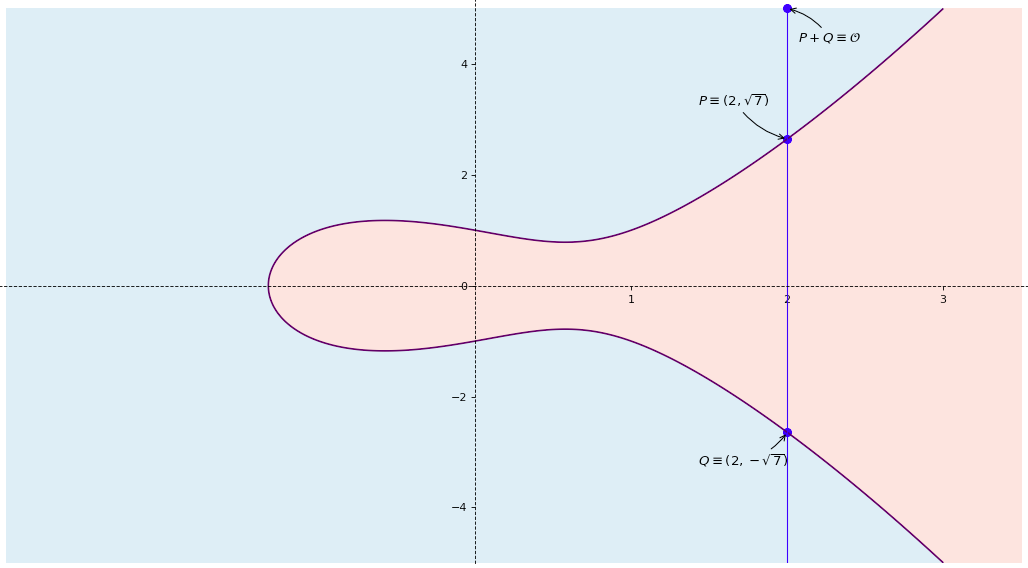
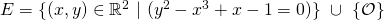
Elliptic curves over ![]() can be easily drawn on the euclidean plane. We include below the graphs of five different elliptic curves, two of which are singular and three regular.
can be easily drawn on the euclidean plane. We include below the graphs of five different elliptic curves, two of which are singular and three regular.
Elliptic curves exhibit x-axis symmetry. To see why, note that ![]() on the curve, it must hold that
on the curve, it must hold that ![]() is also on the curve. Indeed,
is also on the curve. Indeed,
![]()
Moreover, ![]() by virtue of
by virtue of ![]() being a point on the curve. Therefore,
being a point on the curve. Therefore, ![]() demonstrating that
demonstrating that ![]() is also a point on the curve.
is also a point on the curve.
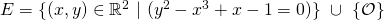
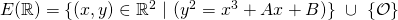
In order to define any group, one needs to have an underlying set of elements as well as a binary operation on it that ensures that the group axioms are observed. In our case, the underlying set contains all the points in the euclidean plane that satisfy the elliptic curve equation. Note that this does not mean that they are the only elements of the set. As a matter of fact, we also include a special point ![]() and refer to it as the point at infinity. We will motivate the introduction of
and refer to it as the point at infinity. We will motivate the introduction of ![]() in the next section. For
in the next section. For ![]() such that
such that ![]() the underlying set of the group takes the form:
the underlying set of the group takes the form:
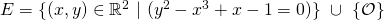
![]()
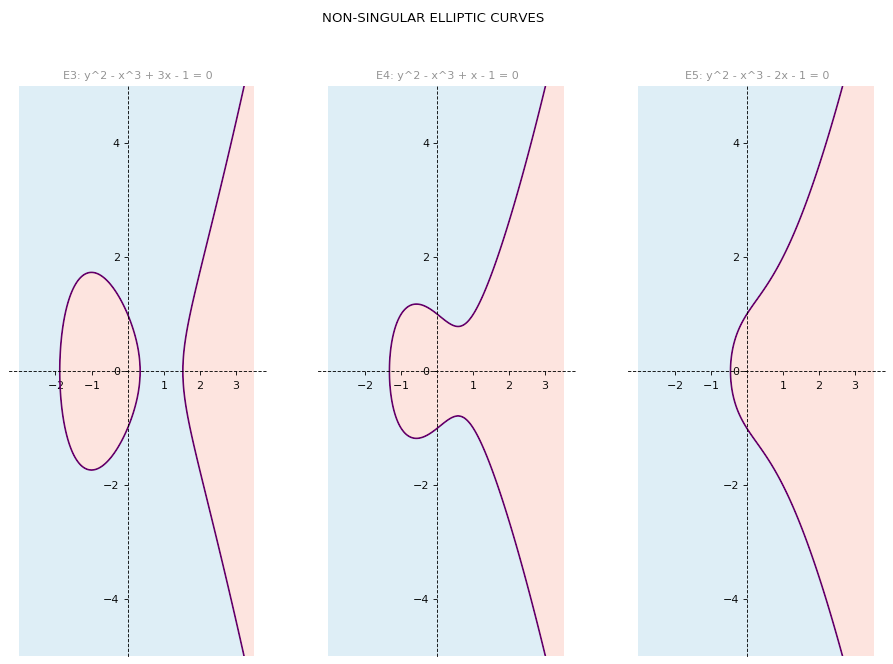
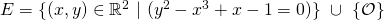
We still need to define a suitable binary operation that acts on a not-necessarily distinct pair of points in ![]() Any group must satisfy the closure axiom and so the output of the binary operation must also be a point in
Any group must satisfy the closure axiom and so the output of the binary operation must also be a point in ![]() Intuitively, the most natural way of geometrically linking two points in the euclidean plane is with a straight line. It is hence reasonable to look at the different configurations of pairs of points on an elliptic curve defined on
Intuitively, the most natural way of geometrically linking two points in the euclidean plane is with a straight line. It is hence reasonable to look at the different configurations of pairs of points on an elliptic curve defined on ![]() The diagram below summarizes the possible scenarios:
The diagram below summarizes the possible scenarios:
It is easy to observe that any two elliptic curve points must belong to one of these categories. As a result, these categories are commonly exhaustive. The configurations are also mutually exclusive. This should be clear except possibly for the case of an inflection point. In what follows we argue that an elliptic curve point with ordinate equals to 0 cannot be an inflection point.
0-ordinate points vs. inflection points: An inflection point ![]() of a curve
of a curve ![]() is one where the curvature changes sign. Without delving deeper into the notion of curvature, this means that the second derivative of
is one where the curvature changes sign. Without delving deeper into the notion of curvature, this means that the second derivative of ![]() with respect to
with respect to ![]() (assuming it exists on a neighborhood of
(assuming it exists on a neighborhood of ![]() ) changes sign as the
) changes sign as the ![]() values cross
values cross ![]() . Intuitively, this suggests the following necessary conditions for a point on the curve (where the second derivative is defined) to be an inflection point:
. Intuitively, this suggests the following necessary conditions for a point on the curve (where the second derivative is defined) to be an inflection point:
- The second derivative
 evaluated at
evaluated at  is equal to 0, and
is equal to 0, and ![Rendered by QuickLaTeX.com sign\ [\frac{d^2(y)}{dx^2}(x_i - \epsilon,f(x_i - \epsilon)] \neq sign\ [\frac{d^2(y)}{dx^2}(x_i + \epsilon,f(x_i + \epsilon)],](https://delfr.com/wp-content/ql-cache/quicklatex.com-dd5f375e94914ca41beb069d52ed0aff_l3.png) for
for  infinitesimally small.
infinitesimally small.
However, an inflection point could still exist even when the second derivative is not defined at that point. The definition remains the same, i.e., an inflection point is one that marks a change in the curve’s concavity. As an example, one can look at the function ![]() defined on
defined on ![]() and verify that the point
and verify that the point ![]() is an inflection point despite the fact that
is an inflection point despite the fact that ![]() is not defined at
is not defined at ![]()
The domain of definition of an elliptic curve over ![]() consists of the set
consists of the set
![]()
This is due to the fact that over the field of real numbers, square values must be non-negative. Consequently, ![]() must be greater than or equal to 0. It then holds that
must be greater than or equal to 0. It then holds that ![]() on
on ![]() As a result:
As a result:
![]()
The second derivative is defined on the set
![]()
Among other things, this means that the second derivative is not defined on curve points whose ordinate is equal to 0. This however, is not enough to justify that 0-ordinate points are not inflection points. To rule out this possibility, we note that by virtue of being a cubic equation, ![]() can admit either one or three roots (not necessarily distinct) in
can admit either one or three roots (not necessarily distinct) in ![]() . We can then classify non-singular elliptic curves on
. We can then classify non-singular elliptic curves on ![]() in two broad categories: disconnected or connected. The figures below showcase an example of each:
in two broad categories: disconnected or connected. The figures below showcase an example of each:
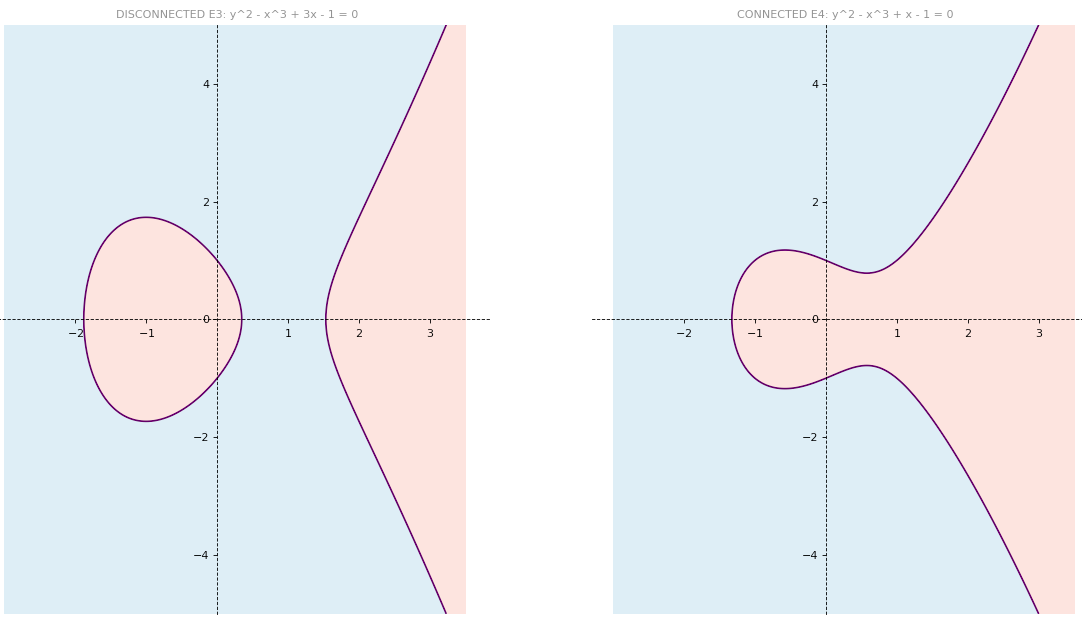
The curve ![]() is an example of a non-singular disconnected curve. These curves admit three distinct real roots, none of which are interior points of the domain of definition
is an example of a non-singular disconnected curve. These curves admit three distinct real roots, none of which are interior points of the domain of definition ![]() (we do not prove this statement). They are boundary points and hence cannot be crossed from right to left or vice-versa. The same applies to the connected curve
(we do not prove this statement). They are boundary points and hence cannot be crossed from right to left or vice-versa. The same applies to the connected curve ![]() which admits one real root instead of three, but whose unique root is also a boundary point of
which admits one real root instead of three, but whose unique root is also a boundary point of ![]()
An implication of the aforestated definition is that the abscissa of an inflection point of a curve in ![]() must be an interior point of
must be an interior point of ![]() Indeed, one should be able to cross it in order to validate a change in curvature. Consequently, points on the elliptic curve of the form
Indeed, one should be able to cross it in order to validate a change in curvature. Consequently, points on the elliptic curve of the form ![]() cannot be inflection points since their abscissas (i.e., the real roots of
cannot be inflection points since their abscissas (i.e., the real roots of ![]() ), are boundary points of
), are boundary points of ![]()
Building the binary operation: Having defined the possible configurations of a pair of points on a non-singular elliptic curve on ![]() we now focus on finding a suitable binary operation. More specifically, given two points on the curve (not-necessarily distinct), our objective is to operate on them in such a way that the output is also a point on the curve.
we now focus on finding a suitable binary operation. More specifically, given two points on the curve (not-necessarily distinct), our objective is to operate on them in such a way that the output is also a point on the curve.
A rather natural way of doing so is to check if the line passing through the two points intersects the curve at another point. In what follows, we consider each configuration separately and demonstrate that the procedure outputs one or two suitable candidate points. We then show that only one of the two points is permissible (whenever they co-exist), paving the way to an algebraic description of the binary operation.
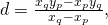
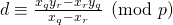
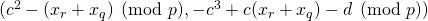
Configuration #1: ![]() and
and ![]() are two distinct points on the elliptic curve such that
are two distinct points on the elliptic curve such that ![]()
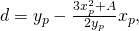
- The equation of the line joining
 and
and  is given by
is given by
We let
 and write
and write 
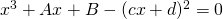
- As a result, any point of intersection of this line with the elliptic curve must have an abscissa that satisfies
- This is a cubic polynomial on
 and as noted earlier, can have either one or three real roots (not necessarily distinct).
and as noted earlier, can have either one or three real roots (not necessarily distinct). - We already know that
 and
and  are two distinct real roots. Consequently, there must exist a third root (not necessarily distinct from the other two) that we denote by
are two distinct real roots. Consequently, there must exist a third root (not necessarily distinct from the other two) that we denote by 
- We write
 which upon expansion shows that
which upon expansion shows that 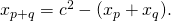
- Consequently,
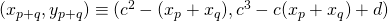 is on the curve due to
is on the curve due to  axis symmetry.
axis symmetry. - Moreover,
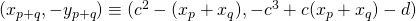 is also on the curve. Later, we specify which of the two points is the eligible one.
is also on the curve. Later, we specify which of the two points is the eligible one. - Here is the graph of an instance of this configuration for the following elliptic curve
Configuration #2: ![]() and
and ![]() are two distinct points on the elliptic curve such that
are two distinct points on the elliptic curve such that ![]() (and hence
(and hence ![]()
- The equation of the line joining
 and
and  is given by
is given by 
- As a result, any point of intersection of this line with the elliptic curve must have an ordinate that satisfies the equation
- This is a quadratic polynomial in
 on
on  It either has no solution or admits two not-necessarily distinct real roots.
It either has no solution or admits two not-necessarily distinct real roots. - We already know that
 and
and  are two distinct roots, and so we concude that these are the only solutions to the equation.
are two distinct roots, and so we concude that these are the only solutions to the equation. - The logic of our construction requires that a viable binary operation involving two roots yield a third one. Consequently, we add the point at infinity to the set of eligible group elements and let
 In this case we only have one elgible candidate as opposed to two.
In this case we only have one elgible candidate as opposed to two. - Here is the graph of an instance of this configuration for the following elliptic curve
Configuration #3: The two points on the elliptic curve are identical and have an ordinate equal to 0. We let the point be denoted by ![]()
- In the case of two distinct points, there was one and only one line that connected them. A single point however, admits an infinity of lines that go through it. A choice must hence be made.
- To do so, imagine that
 is a distinct point on the curve that is infinitesimally close to
is a distinct point on the curve that is infinitesimally close to  In the limit as
In the limit as  approaches
approaches  the line connecting them converges to the line of choice, i.e., the tangent to the elliptic curve at
the line connecting them converges to the line of choice, i.e., the tangent to the elliptic curve at 
- Note that on the domain
 of the elliptic curve,
of the elliptic curve,  Consequently,
Consequently,  on
on  The tangent to the elliptic curve at a 0-ordinate point is a vertical line. In particular, the equation of the tangent at
The tangent to the elliptic curve at a 0-ordinate point is a vertical line. In particular, the equation of the tangent at  is given by
is given by 
- Any point of intersection of this tangent with the elliptic curve must have an ordinate that satisfies the equation
- This is a quadratic polynomial in
 on
on  It either has no solution or admits two not-necessarily distinct real roots.
It either has no solution or admits two not-necessarily distinct real roots. - We already know that
 is a root, hence so is
is a root, hence so is  Consequently 0 is a double root and as a result, the only solution to the equation.
Consequently 0 is a double root and as a result, the only solution to the equation. - Following the same logic of configuration #2, we make use of
 (the point at infinity) and let
(the point at infinity) and let  In this case too, we only have one eligible candidate as opposed to two.
In this case too, we only have one eligible candidate as opposed to two. - Here is the graph of an instance of this configuration for the following elliptic curve
Configuration #4: The two points on the elliptic curve are identical and constitute an inflection point. We let the point be denoted by ![]()
- Following the same logic of configuration #3, we choose the line tangent to the elliptic curve at

- Without loss of generality let
 on
on  Consequently,
Consequently,  on
on 
- Let
 Hence
Hence  The equation of the tangent at
The equation of the tangent at  becomes
becomes 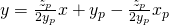
- Any point of intersection of this tangent with the elliptic curve must have coordinates
 that satisfy
that satisfy 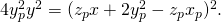 This can be simplified to
This can be simplified to 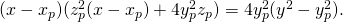
- We claim that this equation admits
 as a triple root. To see why, note that
as a triple root. To see why, note that 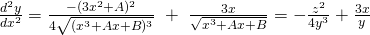 over
over 
- A necessary condition for a point on the curve (where the second derivative is defined) to be an inflection point is that its second derivative be 0. Since
 is such a point, it must be that
is such a point, it must be that 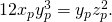 And since
And since  we get
we get 
- Substituting
 with
with  in
in
yields
Since
 we can cancel the
we can cancel the  factor from both sides and obtain
factor from both sides and obtain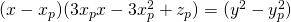
- Substituting
 with
with  and
and  with their
with their  and
and  expressions, we get
expressions, we get
This is equivalent to
- Canceling
 we get
we get 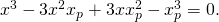 This is equivalent to
This is equivalent to 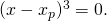 Consequently,
Consequently,  is a triple root.
is a triple root. - Since a cubic equation has a maximum of three roots on
 ,
,  is the only one.
is the only one. - As a result, we could define a binary operation in one of two natural ways:
 or
or  Shortly, we will see why we choose the latter.
Shortly, we will see why we choose the latter. - Here is the graph of an instance of this configuration for the following elliptic curve
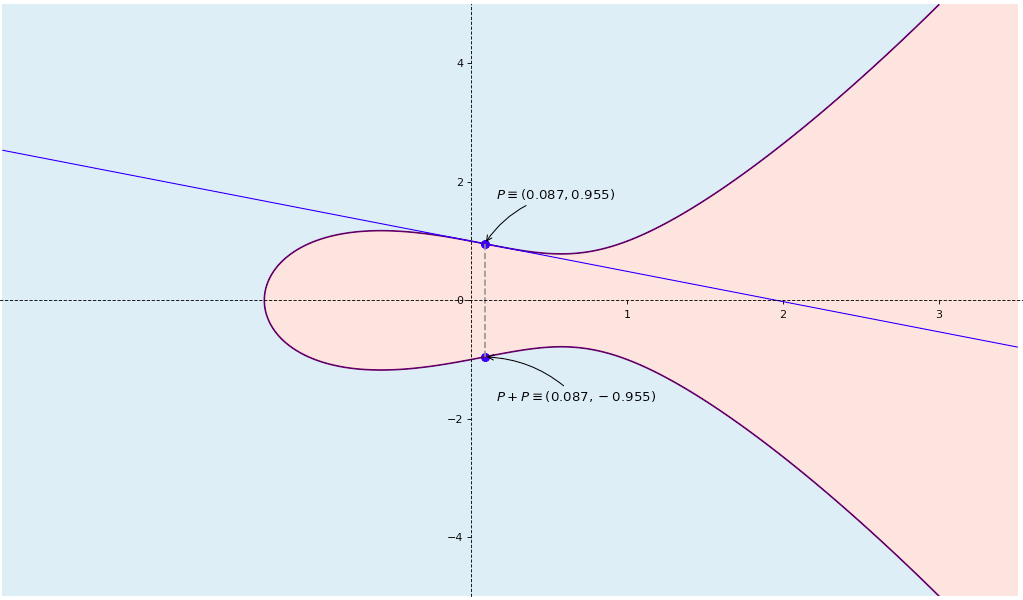
Configuration #5: The two points on the elliptic curve are identical, have non-zero ordinate and are not an inflection point. We let the point be denoted by ![]()
- As in configuration #3, we choose the line tangent to the elliptic curve at

- On
 the tangent’s equation at
the tangent’s equation at  is
is
Letting
 and
and 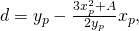 we get
we get 
- As a result, any point of intersection of this line with the elliptic curve must have an abscissa that satisfies
- This is a cubic polynomial on
 and as noted earlier, can have either one or three real roots (not necessarily distinct)
and as noted earlier, can have either one or three real roots (not necessarily distinct) - We know that
 is a double real root, and so there must be a third root. We denote it
is a double real root, and so there must be a third root. We denote it 
- We write
 which upon expansion yields
which upon expansion yields 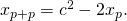
- As a result,
 is on the curve. So is
is on the curve. So is 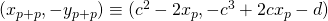 due to
due to  axis symmetry.
axis symmetry. - Note that in configuration #1, if the resulting third root were equal to either
 or
or  (recall that
(recall that  and
and  have distinct absiscas), the outcome would be similar to that of configuration #5.
have distinct absiscas), the outcome would be similar to that of configuration #5. - Here is the graph of an instance of this configuration for the following elliptic curve
Choosing a candidate: In configurations #1, #4 and #5, we ended-up with two points (symmetric about the ![]() -axis) to choose from with regard to the output of the binary operation. Only one of them safeguards the group axioms. To see which one does not, consider configuration #4:
-axis) to choose from with regard to the output of the binary operation. Only one of them safeguards the group axioms. To see which one does not, consider configuration #4:
- Suppose that we choose point
 (as opposed to
(as opposed to  ). That means that
). That means that 
- Consequently,
 must be the identity of the group. We claim that this can not be.
must be the identity of the group. We claim that this can not be. - To see why, choose a curve point
 such that
such that  is not tangent to the curve at
is not tangent to the curve at 
- One can see that this is a special case of configuration #1 (if
 ) or of configuration #2 (if
) or of configuration #2 (if  ), and that the procedure previously described results in candidates all of which are different than
), and that the procedure previously described results in candidates all of which are different than 
- As a result,
 cannot be the identity element and is thus ruled out.
cannot be the identity element and is thus ruled out.
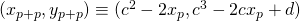
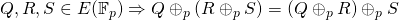
Defining the elliptic curve group: We are now in a position to introduce the elliptic curve group ![]() on
on ![]() and verify that it respects the abelian group axioms.
and verify that it respects the abelian group axioms.
- For given
 such that
such that 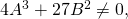 the underlying set of the group is defined to be:
the underlying set of the group is defined to be:
- Let
 and
and  be points in
be points in  . We define the binary operation
. We define the binary operation  as follows:
as follows:
- If
 and
and  (i.e., configuration #1), let
(i.e., configuration #1), let 
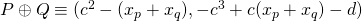
- If
 and
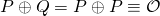
and  (i.e., configuration #2),
(i.e., configuration #2),

- If
 and
and  (i.e., configuration #3),
(i.e., configuration #3),
- If
 and
and  (i.e., configurations #4 and #5), let
(i.e., configurations #4 and #5), let 
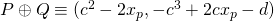
- If
- The point at infinity
 is defined to be the identity element of the elliptic group.
is defined to be the identity element of the elliptic group.
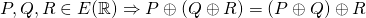
![]() thus defined, satisfies the abelian group axioms:
thus defined, satisfies the abelian group axioms:
- Associativity: Using the aforestated definition of
 one can verify (with a bit of patience and willingness to write down lengthy formulas) that
one can verify (with a bit of patience and willingness to write down lengthy formulas) that
- Existence of identity: We defined
 such that for all
such that for all  we have
we have
Note that for any
 such that
such that 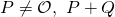 is never equal to
is never equal to  This can be readily verified by checking each configuration separately.
This can be readily verified by checking each configuration separately. - Closure: By construction of
 we made sure that the result of adding two points on the elliptic curve is another point on the curve. In other terms
we made sure that the result of adding two points on the elliptic curve is another point on the curve. In other terms
- Existence of inverse:
 the point
the point  is also in
is also in  This is because the elliptic curve exhibits
This is because the elliptic curve exhibits  -axis symmetry. Moreover,
-axis symmetry. Moreover,  and
and  belong to either configuration #2 (if they are distinct) or configuration #3 (if they are identical) and so the definition of
belong to either configuration #2 (if they are distinct) or configuration #3 (if they are identical) and so the definition of  ensures that
ensures that
As a result,
 is the inverse of
is the inverse of 
- Commutativity: The definition of
 implies that
implies that
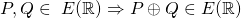
4. Elliptic curve groups over finite fields
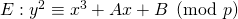
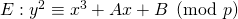
Going forward, we only consider finite fields of prime order ![]() and do not cover extension fields. For an introduction to finite fields, we refer the reader to this post. A non-singular elliptic curve
and do not cover extension fields. For an introduction to finite fields, we refer the reader to this post. A non-singular elliptic curve ![]() defined over a finite field
defined over a finite field ![]() of prime order
of prime order ![]() differs from one defined over
differs from one defined over ![]() in the following way:
in the following way:
- The equation of the curve becomes
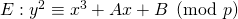 as opposed to
as opposed to 
- The parameters
 and
and  are chosen in
are chosen in  as opposed to
as opposed to 
- The discriminant must satisfy
 as opposed to
as opposed to 
- Points on
 are tuples
are tuples  such that
such that  This is in contrast to tuples
This is in contrast to tuples  such that
such that 
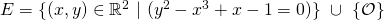
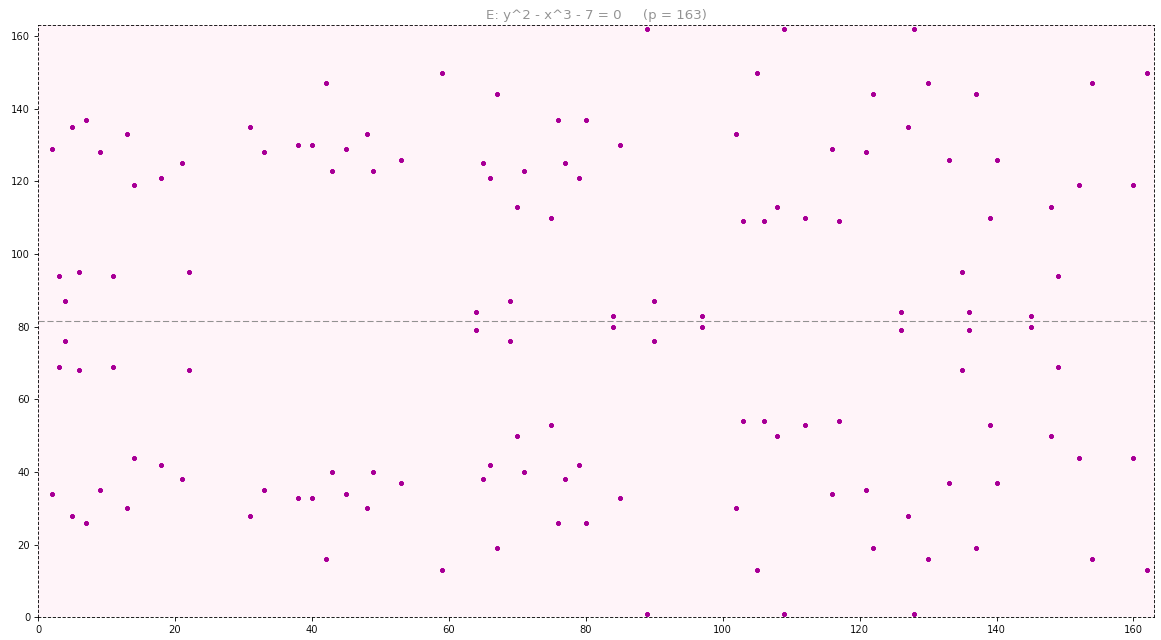
The main difference is that all computations are conducted in modulo ![]() arithmetic. In what follows, we depict the elliptic curve
arithmetic. In what follows, we depict the elliptic curve ![]() over
over ![]() and over
and over ![]() The geometry of elliptic curves over finite fields is not as intuitive as that of those over
The geometry of elliptic curves over finite fields is not as intuitive as that of those over ![]() However, we will see that the algebraic formulation of their associated group closely follows that of elliptic groups over
However, we will see that the algebraic formulation of their associated group closely follows that of elliptic groups over ![]()
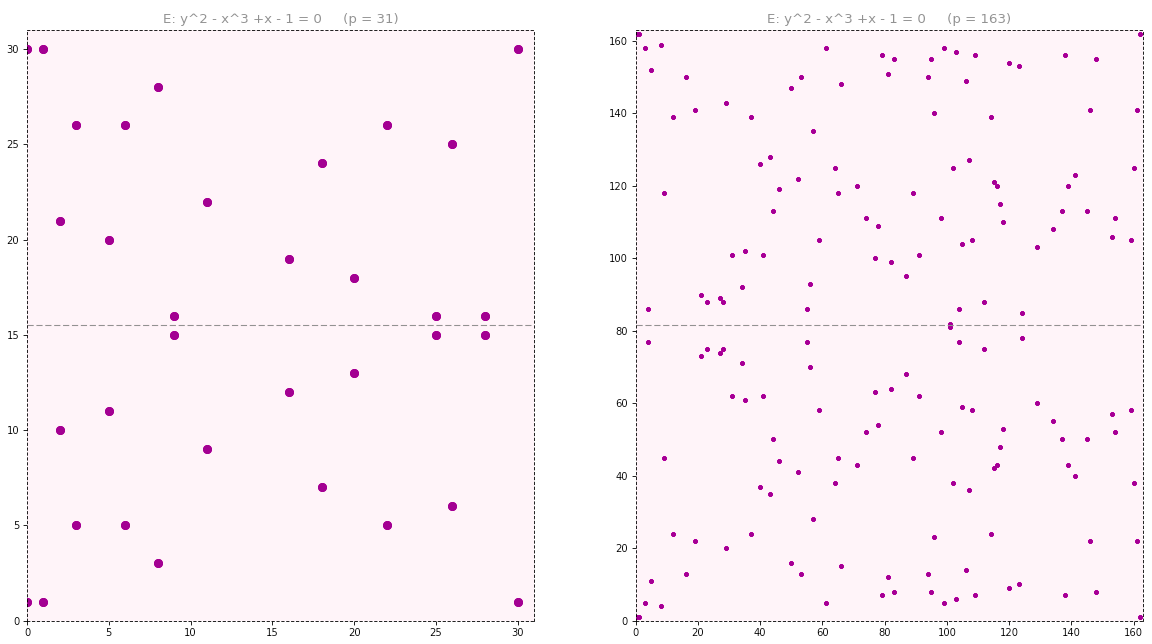
For example, in order to draw ![]() over
over ![]() we select each value of
we select each value of ![]() in the set
in the set ![]() and plug it into the expression
and plug it into the expression ![]() We subsequently check whether the result is a quadratic residue or not by verifying whether
We subsequently check whether the result is a quadratic residue or not by verifying whether ![]() such that
such that ![]() is a match. We find that the euclidean representation of this curve over
is a match. We find that the euclidean representation of this curve over ![]() consists of the following 34 elements:
consists of the following 34 elements:
![]()
![]()
![]()
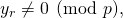
While on ![]() the elliptic curve exhibited
the elliptic curve exhibited ![]() -axis symmetry, on
-axis symmetry, on ![]() it exhibits symmetry about the horizontal line
it exhibits symmetry about the horizontal line ![]() Indeed, if
Indeed, if ![]() is a point on the curve, then so will
is a point on the curve, then so will ![]() This is because
This is because ![]()
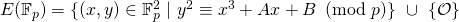
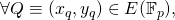
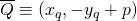
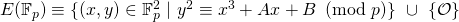
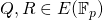
Formally, we denote by ![]() the group associated with an elliptic curve defined over
the group associated with an elliptic curve defined over ![]() In particular:
In particular:
- For
 and
and  such that
such that  the underlying set of the group is defined to be:
the underlying set of the group is defined to be:
- Let
 and
and  be points in
be points in  . We define the binary operation
. We define the binary operation  as follows:
as follows:
- If
 and
and 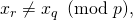 let
let 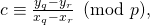
 (division refers to multiplication by the inverse of the denominator over
(division refers to multiplication by the inverse of the denominator over  ,
,

- If
 and
and 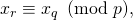

- If
 and
and 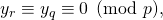
- If

 let
let 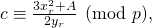
 (division means multiplication by the inverse of the denominator over
(division means multiplication by the inverse of the denominator over 
- If
- The point at infinity
 is defined to be the identity element of the elliptic group.
is defined to be the identity element of the elliptic group.
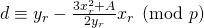
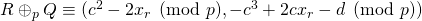
To illustrate point addition in elliptic curve groups over finite fields, we look at ![]() and operate on points
and operate on points ![]() and
and ![]() Since
Since ![]() and
and ![]() we compute
we compute
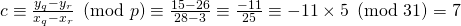
where 5 is the inverse of 25 in modulo 31 arithmetic (recall that this can be efficiently computed using the extended euclidean algorithm introduced in the Groups and Finite Fields post).
-
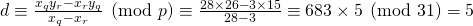
We then compute
![]()
![]()
The construction of ![]() is similar to that of
is similar to that of ![]() except for the fact that values are computed modulo
except for the fact that values are computed modulo ![]()
![]() thus defined, satisfies the abelian group axioms:
thus defined, satisfies the abelian group axioms:
- Associativity: Using the aforestated definition of
 one can verify after lengthy and tedious calculations that
one can verify after lengthy and tedious calculations that
- Existence of identity: We defined
 such that for all
such that for all  we have
we have
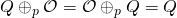
- Closure: By definition of
 the resulting output is either
the resulting output is either  or a tuple
or a tuple  (since all arithmetic is conducted modulo
(since all arithmetic is conducted modulo  ). Moreover, one can readily use the definition of
). Moreover, one can readily use the definition of  to check that the result of the binary operation always verifies the elliptic curve equation modulo
to check that the result of the binary operation always verifies the elliptic curve equation modulo  . Consequently,
. Consequently,
- Existence of inverse:
 is also in
is also in  due to symmetry about the line
due to symmetry about the line  . And so the definition of
. And so the definition of  ensures that
ensures that
As a result,
 is the inverse of
is the inverse of 
- Commutativity: The definition of
 implies that
implies that
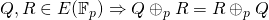
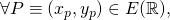
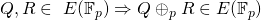
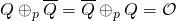
ECDLP, cardinality, and point multiples in ![]() Recall that the importance of elliptic curve groups over finite fields is largely derived from the exponential hardness of the DL problem on them. The Elliptic Curve Discrete Logarithm Problem (also known as ECDLP) can be stated as follows:
Recall that the importance of elliptic curve groups over finite fields is largely derived from the exponential hardness of the DL problem on them. The Elliptic Curve Discrete Logarithm Problem (also known as ECDLP) can be stated as follows:
- Let
 be an elliptic curve defined over a finite field
be an elliptic curve defined over a finite field  (i.e.,
(i.e.,  such that
such that 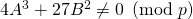 )
)
- Let
 be the group associated with it, where
be the group associated with it, where
- Let
 and find the smallest integer
and find the smallest integer  (if it exists) such that
(if it exists) such that
 (
( times)
times)
The notation ![]() is unusual as it is commonly written as
is unusual as it is commonly written as ![]() We decide to make explicit the appearance of the operator
We decide to make explicit the appearance of the operator ![]() as a reminder that it is scalar multiplication with respect to the binary operator
as a reminder that it is scalar multiplication with respect to the binary operator ![]()
Finding such an ![]() when it exists is thought to be exponentially hard. In the context of crypto-assets, we don’t operate on the full set
when it exists is thought to be exponentially hard. In the context of crypto-assets, we don’t operate on the full set ![]() Rather, we choose an element
Rather, we choose an element ![]() such that order(
such that order(![]() ) is a very large prime. We then limit ourselves to the subgroup
) is a very large prime. We then limit ourselves to the subgroup ![]() generated by
generated by ![]() (refer to the post on Groups and Finite Fields for an introduction to subgroups). Given
(refer to the post on Groups and Finite Fields for an introduction to subgroups). Given ![]() and
and ![]() ECDLP now consists in finding the smallest integer
ECDLP now consists in finding the smallest integer ![]() such that
such that ![]() We are confident that such an
We are confident that such an ![]() exists since
exists since ![]()
In the digital signature schemes used in e.g., Bitcoin and Monero, ![]() represents the private key and
represents the private key and ![]() the public one. It is important to derive
the public one. It is important to derive ![]() efficiently from
efficiently from ![]() However, as we stated earlier, it must not be polynomially feasible to compute
However, as we stated earlier, it must not be polynomially feasible to compute ![]() from
from ![]() . The exponential hardness of ECDLP helps with the latter requirement. Moreover, one can expect that the larger the set
. The exponential hardness of ECDLP helps with the latter requirement. Moreover, one can expect that the larger the set ![]() the better. This justifies the importance of having a sense of the cardinality of
the better. This justifies the importance of having a sense of the cardinality of ![]() also denoted
also denoted ![]() In order to ensure the former requirement, we need to have an efficient polynomial-time algorithm that can compute multiples of
In order to ensure the former requirement, we need to have an efficient polynomial-time algorithm that can compute multiples of ![]()
- Cardinality of
 : We previously saw (e.g., in the case of
: We previously saw (e.g., in the case of  ) that not every tuple
) that not every tuple  is necessarily an element of
is necessarily an element of  . To get an upper-bound on
. To get an upper-bound on  note that for every
note that for every  one can have at most two values of
one can have at most two values of  that satisfy the elliptic curve equation
that satisfy the elliptic curve equation
If
 is a solution, then so will
is a solution, then so will  In addition, we have the point at infinity
In addition, we have the point at infinity  As a result, since there are
As a result, since there are  distinct values in
distinct values in  we get a maximum of
we get a maximum of  points in
points in  Over
Over  there are
there are  quadratic residues and an equal number of quadratic non-residues (we don’t prove this statement in this post). As a result, in the absence of any information, a random
quadratic residues and an equal number of quadratic non-residues (we don’t prove this statement in this post). As a result, in the absence of any information, a random  has equal probability of being a square or not. One can then calculate the expected value of the number of points in
has equal probability of being a square or not. One can then calculate the expected value of the number of points in  to be
to be 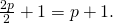 The German mathematician Helmut Hasse showed that
The German mathematician Helmut Hasse showed that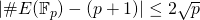
The Dutch mathematician René Schoof, relied partly on Hasse’s theorem to devise a deterministic algorithm that can compute
 with complexity
with complexity  This is known as the Schoof algorithm and its proof is beyond the scope of this post (readers interested in learning more about it can consult [9]). The important take-away is that there exists a polynomial-time algorithm to calculate the order of an elliptic curve group over a finite field.
This is known as the Schoof algorithm and its proof is beyond the scope of this post (readers interested in learning more about it can consult [9]). The important take-away is that there exists a polynomial-time algorithm to calculate the order of an elliptic curve group over a finite field.In so far as the structure of this group is concerned, we mention without proof that
 is always either cyclic or the product of two cyclic groups.
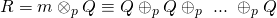
is always either cyclic or the product of two cyclic groups. - Point multiplicity: Suppose
 is a very large integer, and
is a very large integer, and  is as defined earlier. In order to calculate
is as defined earlier. In order to calculate 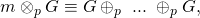 one can do the following:
one can do the following:
- Write
 in its base 2 expansion
in its base 2 expansion
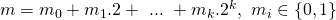 for
for 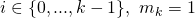
This can be achieved in

- Subsequently, write
 as
as
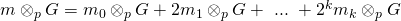
 for
for 
- Since the value
 is equal to
is equal to  can be evaluated by doubling the point
can be evaluated by doubling the point  (i.e.,
(i.e.,  then
then  ) a total of
) a total of  times. In the process, we store the value of
times. In the process, we store the value of  for all
for all  for which
for which 
- Putting it altogether, in order to caculate
 one first needs
one first needs  steps to find
steps to find  then a total of
then a total of  point doublings, and finally, a worst-case total of
point doublings, and finally, a worst-case total of  additions. Hence, the worst-case complexity is
additions. Hence, the worst-case complexity is  Noting that
Noting that  is on the order of
is on the order of  the complexity becomes
the complexity becomes  The above procedure is known as the double-and-add method and ensures that point addition can be efficiently carried on elliptic curves over finite fields.
The above procedure is known as the double-and-add method and ensures that point addition can be efficiently carried on elliptic curves over finite fields.
- Write
- A note on finding
 : A question of practical importance is whether one can efficiently find an adequate point
: A question of practical importance is whether one can efficiently find an adequate point  such that its order is equal to a large prime. This question is justified since finite fields of interst have an astronomically large characteristic (usually larger that
such that its order is equal to a large prime. This question is justified since finite fields of interst have an astronomically large characteristic (usually larger that  ) and one cannot expect to conduct an exhaustive search on the underlying group. The answer turns out to be positive, and one way of finding a suitable
) and one cannot expect to conduct an exhaustive search on the underlying group. The answer turns out to be positive, and one way of finding a suitable  is as follows:
is as follows:
- Calculate
 using Schoof’s polynomial-time algorithm.
using Schoof’s polynomial-time algorithm. - Find a very large prime (ideally the largest)
 that divides
that divides  Say
Say  Note that the integer factorization problem is thought to be hard. However, in some cases where the integer exhibits certain properties, one can employ more efficient algorithms to identify a prime factor. We will not go into the details of these algorithms but refer the interested reader to e.g., [4] for an accessible overview.
Note that the integer factorization problem is thought to be hard. However, in some cases where the integer exhibits certain properties, one can employ more efficient algorithms to identify a prime factor. We will not go into the details of these algorithms but refer the interested reader to e.g., [4] for an accessible overview. - Choose a random point
 We know that order
We know that order order
order . By Lagrange’s theorem, the order of any subgroup divides the order of the parent group. As a result, the order of
. By Lagrange’s theorem, the order of any subgroup divides the order of the parent group. As a result, the order of  must divide
must divide  and so
and so
- Consequently, the order of the element
 must divide
must divide  Since
Since  is prime, the order of
is prime, the order of  can either be equal to 1 or
can either be equal to 1 or  If it is 1, then
If it is 1, then  is the identity element
is the identity element  In this case, we go back to step 3 and choose a different point
In this case, we go back to step 3 and choose a different point  Otherwise, we set
Otherwise, we set  which can be computed efficiently using the aforementioned double-and-add method. We refer to
which can be computed efficiently using the aforementioned double-and-add method. We refer to  as the cofactor of
as the cofactor of 
- Calculate
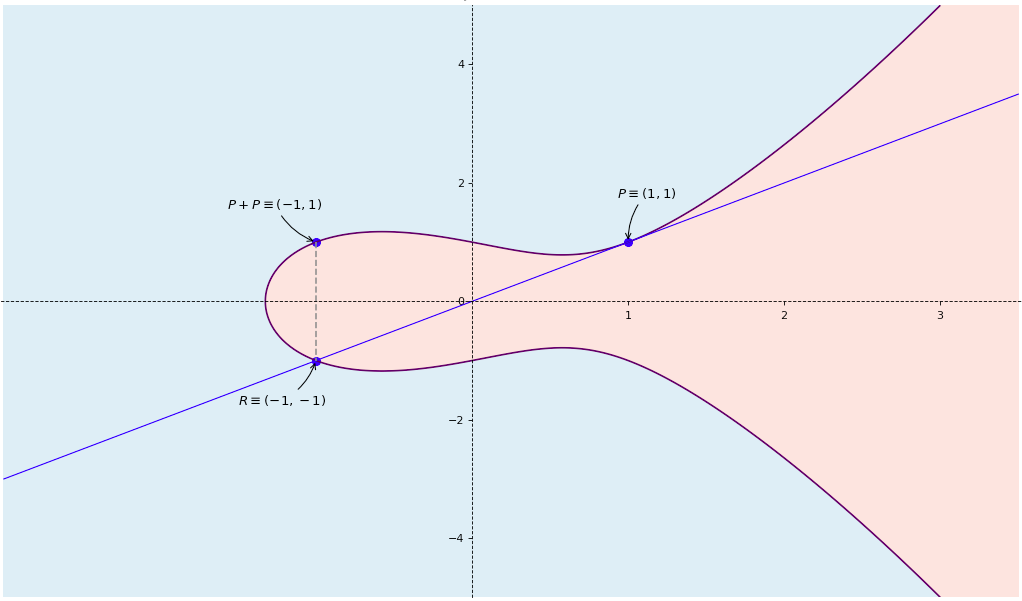
5. Elliptic curve in Bitcoin
Bitcoin’s cryptography relies on a particular curve known as secp256k1:
- “sec” is short for Standard for Efficient Cryptography. It refers to a set of standards developed by the Certicom Research consortium [7].
- “p” refers to the fact that the curve is defined over a finite field
 of prime order
of prime order 
- “256” means that the curve points’ abscissas and ordinates are 256-bit long.
- “k” states that the curve belongs to the Koblitz family. Usually, Koblitz curves are defined over extension fields of characteristic 2 i.e., over
 for some positive integer
for some positive integer  However, the Bitcoin curve is defined over a prime field of characteristic
However, the Bitcoin curve is defined over a prime field of characteristic  It belongs to a more general version of Koblitz curves. Without going into further details, it suffices to say that for all practical matters, the importance of this class of curves is derived from its higher efficiency in computing point multiples on its associated group.
It belongs to a more general version of Koblitz curves. Without going into further details, it suffices to say that for all practical matters, the importance of this class of curves is derived from its higher efficiency in computing point multiples on its associated group. - “1” is a reminder that it is the first curve of its kind that satisfies the previous attributes.
The parameters of secp256k1 can be found on page 9 of [7] and are as follows:
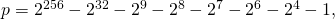 or in hexadecimal notation (hex)
or in hexadecimal notation (hex)
FFFFFFFF FFFFFFFF FFFFFFFF FFFFFFFF FFFFFFFF FFFFFFFF FFFFFFFE FFFFFC2F
Each element represents a half-byte (i.e., 4 bits) known as a nibble. There are 64 nibbles corresponding to the 256-bit representation mandated by the standard.
 which in standard hex is given by
which in standard hex is given by
00000000 00000000 00000000 00000000 00000000 00000000 00000000 00000000
 which in standard hex is given by
which in standard hex is given by
00000000 00000000 00000000 00000000 00000000 00000000 00000000 00000007
- Since
 and
and 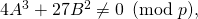 the curve is non-singular and can be written in short Weierstrass form. The resulting group is
the curve is non-singular and can be written in short Weierstrass form. The resulting group is  where
where
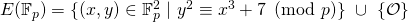
Here is a euclidean representation of this curve when
 (it is not feasible to show it for
(it is not feasible to show it for 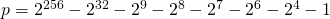 ):
):
- The base point
 has abscissa and ordinate given by
has abscissa and ordinate given by


which in standard hex notation are given by:
 79BE667E F9DCBBAC 55A06295 CE870B07 029BFCDB 2DCE28D9 59F2815B 16F81798
79BE667E F9DCBBAC 55A06295 CE870B07 029BFCDB 2DCE28D9 59F2815B 16F81798 483ADA77 26A3C465 5DA4FBFC 0E1108A8 FD17B448 A6855419 9C47D08F FB10D4B8
483ADA77 26A3C465 5DA4FBFC 0E1108A8 FD17B448 A6855419 9C47D08F FB10D4B8Bitcoin’s public-key cryptography is hence conducted on the subgroup

- The order of
 is chosen to be a prime number equal to
is chosen to be a prime number equal to

which in standard hex notation is given by
 FFFFFFFF FFFFFFFF FFFFFFFF FFFFFFFE BAAEDCE6 AF48A03B BFD25E8C D0364141
FFFFFFFF FFFFFFFF FFFFFFFF FFFFFFFE BAAEDCE6 AF48A03B BFD25E8C D0364141 - Recall that
 denotes the order of
denotes the order of  and must divide
and must divide  i.e., the order of
i.e., the order of  . The cofactor
. The cofactor  is equal to
is equal to  which in this case is equal to 1 and is represented in standard hex notation by
which in this case is equal to 1 and is represented in standard hex notation by
 0000000 00000000 00000000 00000000 00000000 00000000 00000000 00000001
0000000 00000000 00000000 00000000 00000000 00000000 00000000 00000001That means that the order of
 is equal to that of
is equal to that of  i.e.,
i.e.,  Since
Since  is prime, the order of
is prime, the order of  must also be prime. As a result,
must also be prime. As a result,  is a cyclic group and any of its elements could serve as a generator (refer to Groups and Finite Fields for an introduction to cyclic groups).
is a cyclic group and any of its elements could serve as a generator (refer to Groups and Finite Fields for an introduction to cyclic groups).
Another noteworthy SEC2 curve is secp256r1. The “r” specifier refers to the attribute “random” since the generation of the curve parameters ![]() and
and ![]() relies on a supposedly random process involving a seed value fed to a hash function. The seed value as well as the other curve attributes can be found on pages 9 and 10 of [7].
relies on a supposedly random process involving a seed value fed to a hash function. The seed value as well as the other curve attributes can be found on pages 9 and 10 of [7].
There was a fair amount of questioning as to why Satoshi opted for the usage of secp256k1 as opposed to that of another curve such as secp256r1. The reason(s) remain obscure and advocates that favor one curve over the other abound (e.g., [5], [1]). The point of contention lies in the randomness involved in selecting the curve parameters:
- On the one hand, Koblitz curves exhibit slightly weaker security than other curves (although when using 256-bit long parameters, the difference is negligible). Moreover, the National Institute of Standards and Technology or NIST (a US governmental agency) has been advocating the usage of secp256r1 on the basis that its parameters achieve very high security standards. Another common name of this curve is NIST P-256, and constitutes one of fifteen curves that NIST recommends.
- On the other hand, skeptics argue that NIST’s endorsement, coupled with the absence of a rationale for the choice of the seed value are ground for dismissal. According to them, it is possible that the NIST (and affiliated entities) might have placed a backdoor to weaken the curve’s security standard. Their scepticism is not unfounded since the NSA and NIST have previously planted a backdoor in the elliptic curve algorithm known as Dual_EC_DRBG, which was validated by memos leaked by Edward Snowden. The interested reader can refer to [11] for a take on how the NSA might have accomplished this.
Suffice it to say that no one can tell with certainty whether one curve is preferred over the other. Assuming no backdoor, both curves exhibit comparable security standards.
6. Elliptic curve in Monero
The NIST debacle surrounding the Dual_EC_DRBG algorithm pushed some people away from NIST curves and closer to curves generated in academic circles instead. Two such curves are Curve25519 and its next of kin ed25519 used in Monero. Both are elliptic curves, but are not represented in short Weierstrass form. However, they could be transformed into one and we will see how shortly.
Curve25519 was originally introduced by the German-American mathematician and cryptologist Daniel Julius Bernstein. Unlike SEC curves and some of those advocated by NIST, Curve25519 is thougt to be patent-free. It is also hailed for its faster computation of point multiples when compared to e.g., sec256r1 (NIST P-256) [6]. Moreover, it exhibits a security level comparable to that of secp256k1 and secp256r1 (assuming no backdoors). These favorable attributes paved the way for its ever-increasing adoption.
We first provide an overview of Montgomery and Twisted Edward representations of elliptic curves of which Curve25519 and ed25519 are respective examples. We show that under certain constraints, any of these representations could be transformed into a short Weierstrass counterpart using a specific isomorphism. The existence of an isomorphism makes the two curves’ respective groups equivalent and guarantees that the hardness of ECDLP is preserved on both. In the last section, we introduce the attributes of Monero’s ed25519 curve.
Twisted Edward and Montgomery representations: A Twisted Edward curve defined on a field ![]() such that
such that ![]() with parameters
with parameters ![]() and
and ![]() such that
such that ![]() is one that satisifies the following equation
is one that satisifies the following equation
![]()
It turns out that if in addition, ![]() is a square in
is a square in ![]() and
and ![]() is not, the curve will define a group structure. For our purposes, on a finite field
is not, the curve will define a group structure. For our purposes, on a finite field ![]() such a curve will define a group
such a curve will define a group ![]() where the superscript
where the superscript ![]() refers to “Edward”. One could define the binary operation
refers to “Edward”. One could define the binary operation ![]() from basic principles as we did earlier for curves in short Weierstrass form. However, we show shortly that each such Twisted Edward curve is equivalent to another one in short Weierstrass form. The equivalence implicitly defines a corresponding group structure associated with it. The underlying set of the group is defined as
from basic principles as we did earlier for curves in short Weierstrass form. However, we show shortly that each such Twisted Edward curve is equivalent to another one in short Weierstrass form. The equivalence implicitly defines a corresponding group structure associated with it. The underlying set of the group is defined as
![]()
Note that it does not contain a point at infinity. We will attempt to justify its absence when we discuss the equivalence betwen curve representations.
A Montgomery curve defined on a field ![]() such that
such that ![]() with given parameters
with given parameters ![]() and
and ![]() such that
such that ![]() is one that satisifies the following equation
is one that satisifies the following equation
![]()
The curve thus defined, admits a group structure assoiated with it. For our purposes, on a finite field ![]() this curve defines a group
this curve defines a group ![]() where the superscript
where the superscript ![]() refers to “Montgomery”. Here too, one could define the binary operation
refers to “Montgomery”. Here too, one could define the binary operation ![]() from basic principles using the chord and tangent method presented earlier for Weierstrass curves in short form. However, we show shortly that every Montgomery curve is equivalent to another one in short Weierstrass form. As is the case for Twisted Edward curves, this equivalence implicitly defines a corresponding group structure associated with it. The underlying set of the group is defined as
from basic principles using the chord and tangent method presented earlier for Weierstrass curves in short form. However, we show shortly that every Montgomery curve is equivalent to another one in short Weierstrass form. As is the case for Twisted Edward curves, this equivalence implicitly defines a corresponding group structure associated with it. The underlying set of the group is defined as
![]()
Note that it contains a point at infinity denoted by ![]() . The need for such a point will be addressed when we discuss the equivalence betwen curve representations.
. The need for such a point will be addressed when we discuss the equivalence betwen curve representations.
Every Montgomery curve is equivalent to a short Weierstrass one: Starting with a Montgomery curve
![]()
where ![]() (we will justify this constraint shortly), our objective is to transform it into a short-form Weierstrass curve
(we will justify this constraint shortly), our objective is to transform it into a short-form Weierstrass curve
![]()
where the superscript ![]() refers to Weierstrass. Moreover,
refers to Weierstrass. Moreover, ![]() must be different than 2 or 3 for the short Weierstrass form to hold, and
must be different than 2 or 3 for the short Weierstrass form to hold, and ![]() different than
different than ![]() for it to be non-singular.
for it to be non-singular.
The sought after transformation must map every point ![]() on
on ![]() to a point
to a point ![]() on
on ![]() . Let’s first exclude the point at infinity of
. Let’s first exclude the point at infinity of ![]() and focus on the other points. Let’s substitute
and focus on the other points. Let’s substitute ![]() with
with ![]() and
and ![]() with
with ![]() This yields
This yields
![]()
![]()
![]()
![]()
In order to make the coefficient of ![]() equal to 1 (as mandated by the short Weierstrass form), it must be that
equal to 1 (as mandated by the short Weierstrass form), it must be that ![]() so that we can multiply both sides of the equation by the modular inverse of
so that we can multiply both sides of the equation by the modular inverse of ![]() We get
We get
![]()
![]()
We recognize a short Weierstrass form with ![]() and
and ![]() For it to be valid, we still need to ensure that
For it to be valid, we still need to ensure that ![]() This means that
This means that
![]()
![]()
The constraints ![]() and
and ![]() can be combined into a single one given by
can be combined into a single one given by ![]() This explains its inclusion earlier when we defined the Montgomery form.
This explains its inclusion earlier when we defined the Montgomery form.
The above derivation mapped every point of the Montgomery curve to a point on the short-Weierstrass curve. Note that the point at inifnity ![]() of the short-Weierstrass form was not attained by the previous transformation. As a result, we define a point at infinity
of the short-Weierstrass form was not attained by the previous transformation. As a result, we define a point at infinity ![]() on the Montgomery curve and map it to
on the Montgomery curve and map it to ![]() Consequently, we get the following injective map:
Consequently, we get the following injective map:
![]()
![]() if
if ![]()
![]()
In order to show that this map is a bijection, we must demonstrate that it has an inverse. We claim that given ![]() such that
such that ![]() the short Weierstrass form
the short Weierstrass form ![]() can be transformed into the Montgomery curve
can be transformed into the Montgomery curve ![]() Here, parameters
Here, parameters ![]() and
and ![]() are respectively given by
are respectively given by ![]() and
and ![]()
This can be readily verified by substituting ![]() with
with ![]() and
and ![]() with
with ![]() This substitution shows that every point on the given short Weierstrass form is mapped to a point on the Montgomery curve. The only point left out is
This substitution shows that every point on the given short Weierstrass form is mapped to a point on the Montgomery curve. The only point left out is ![]() which we then map to
which we then map to ![]() As a result, we get the following inverse transformation:
As a result, we get the following inverse transformation:
![]()
![]() if
if ![]()
![]()
Note that with the exception of ![]() and
and ![]() the map
the map ![]() (and its inverse) have their two components expressed as a rational fraction in
(and its inverse) have their two components expressed as a rational fraction in ![]() Such transformations are known as birational maps. As a result, the bijection between a Montgomery form and its associated short Weierstrass form is also referred to as a birational equivalence. One important observation is that any Montgomery form can be transformed into a short Weierstrass curve. However, the reverse is not always possible. We will not define the constraints that must be imposed on a short Weierstrass curve to admit a Montgomery counterpart. Suffice it to say that the specific values of
Such transformations are known as birational maps. As a result, the bijection between a Montgomery form and its associated short Weierstrass form is also referred to as a birational equivalence. One important observation is that any Montgomery form can be transformed into a short Weierstrass curve. However, the reverse is not always possible. We will not define the constraints that must be imposed on a short Weierstrass curve to admit a Montgomery counterpart. Suffice it to say that the specific values of ![]() and
and ![]() previously used satisfy the required constraints.
previously used satisfy the required constraints.
Equivalence of (certain) Twisted Edward and (certain) Montgomery curves: Starting with a Twisted Edward curve
![]()
where ![]() and requiring additionally that
and requiring additionally that ![]() be a quadratic residue over
be a quadratic residue over ![]() and
and ![]() a quadratic non-residue (we will justify these constraints shortly), our objective is to transform it into a Montgomery curve given by
a quadratic non-residue (we will justify these constraints shortly), our objective is to transform it into a Montgomery curve given by
![]()
where ![]() This is equivalent to
This is equivalent to ![]() and
and ![]()
The transformation must map every point ![]() on
on ![]() to a point
to a point ![]() on
on ![]() To do so, let’s substitute
To do so, let’s substitute ![]() with
with ![]() and
and ![]() with
with ![]() This substitution attains every point on the Montgomery curve except for the following points:
This substitution attains every point on the Montgomery curve except for the following points:
- The point at infinity

- Points with
 The equation of a Montgomery elliptic curve would then dictate that
The equation of a Montgomery elliptic curve would then dictate that  This in turn means that
This in turn means that  or
or  To minimize the number of points on the Montgomery curve that are not attained, we require that the quadratic equation
To minimize the number of points on the Montgomery curve that are not attained, we require that the quadratic equation  admit no solution in
admit no solution in  In order to ensure that, the discriminant
In order to ensure that, the discriminant  must be a quadratic non-residue over
must be a quadratic non-residue over  Consequently, the only point to exclude from the Montgomery curve in this case is
Consequently, the only point to exclude from the Montgomery curve in this case is 
- Points with
 The equation of a Montgomery elliptic curve would then dictate that
The equation of a Montgomery elliptic curve would then dictate that  Since
Since  this becomes
this becomes  To minimize the number of points on the Montgomery curve that are not attained, we require that
To minimize the number of points on the Montgomery curve that are not attained, we require that  also be a quadratic non-residue over
also be a quadratic non-residue over 
The change of variable dictates that if ![]() then
then ![]() Consequently, we must exclude the points on the Twisted Edward curve that have
Consequently, we must exclude the points on the Twisted Edward curve that have ![]() One can readily verify that these are the points
One can readily verify that these are the points ![]() and
and ![]() So let’s apply the variable substitution, keeping these two points out for now. We will treat them separately in a moment.
So let’s apply the variable substitution, keeping these two points out for now. We will treat them separately in a moment.
![]()
![]()
And since we excluded the cases ![]() and
and ![]() we get
we get
![]()
![]()
Since ![]() we can multiply both sides of the equation by the modular inverse of
we can multiply both sides of the equation by the modular inverse of ![]() and get
and get
![]()
To ensure that the coefficient of ![]() is equal to 1 as mandated by the Montgomery form, we must have
is equal to 1 as mandated by the Montgomery form, we must have ![]() so that we can multiply both sides of the equation by the modular inverse of
so that we can multiply both sides of the equation by the modular inverse of ![]() In this case, we obtain
In this case, we obtain
![]()
We recognize the Montgomery elliptic curve form with ![]() and
and ![]() However, we must still make sure that
However, we must still make sure that ![]() as mandated by the definition of a Montgomery form. Clearly,
as mandated by the definition of a Montgomery form. Clearly, ![]() We only need to make sure that
We only need to make sure that ![]() This translates to
This translates to ![]() which implies that
which implies that ![]()
To sum-up, the variable substitution that we introduced defines a map from ![]() to
to ![]() given by
given by ![]() The constraints that need to be observed are the following:
The constraints that need to be observed are the following:
 must be a quadratic non-residue over
must be a quadratic non-residue over  In terms of the Twisted Edward curve parameters
In terms of the Twisted Edward curve parameters  and
and  this translates to
this translates to 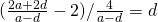 being a quadratic non-residue.
being a quadratic non-residue.- (
 ) must be a quadratic non-residue over
) must be a quadratic non-residue over  This means that
This means that ![Rendered by QuickLaTeX.com [(\frac{2a+2d}{a-d})^2 - 4]](https://delfr.com/wp-content/ql-cache/quicklatex.com-e2fba58f894fc25145d6aac139342592_l3.png) is a quadratic non-residue. Consequently,
is a quadratic non-residue. Consequently,  must be a quadratic non-residue. Since 16 and
must be a quadratic non-residue. Since 16 and  are both quadratic residues, it must be that
are both quadratic residues, it must be that  is a quadratic non-residue. Now note that if both
is a quadratic non-residue. Now note that if both  and
and  were squares, then so will
were squares, then so will  Moreover, if
Moreover, if  and
and  were both non-squares, there could still be a possibility that
were both non-squares, there could still be a possibility that  is a square (as an example, take the elements 3 and 5 over
is a square (as an example, take the elements 3 and 5 over  which are both quadratic non-residues but their product is a square). As a result, we require that if
which are both quadratic non-residues but their product is a square). As a result, we require that if  is a square then
is a square then  be not and vice-versa. Since we saw that
be not and vice-versa. Since we saw that  is a quadratic non-residue, then we require that
is a quadratic non-residue, then we require that  be a quadratic residue.
be a quadratic residue. 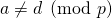 and
and 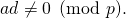 We can combine both constraints into a single one
We can combine both constraints into a single one 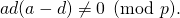
Finally, note that we left out two points on the Twisted Edward curve, namely ![]() and
and ![]() Observe however, that on the Montgomery elliptic curve, we also have two points that were not covered, namey the point
Observe however, that on the Montgomery elliptic curve, we also have two points that were not covered, namey the point ![]() and the point at infinity
and the point at infinity ![]() We thus define the following injective transformation:
We thus define the following injective transformation:
![]()
![]() , if
, if ![]()
![]()
![]()
Conversely, starting with the Montgomery curve
![]()
where ![]() (
(![]() ) and (
) and (![]() ) are both quadratic non-residues over
) are both quadratic non-residues over ![]() we can show that it can be transformed into a Twisted Edward curve of the form
we can show that it can be transformed into a Twisted Edward curve of the form
![]()
where ![]()
To do so, we make use of the inverse of the previous substitution. We substitute ![]() with
with ![]() and
and ![]() with
with ![]() Clearly, these are defined for all points
Clearly, these are defined for all points ![]() as long as
as long as ![]() and
and ![]() But note that
But note that ![]() corresponds to
corresponds to ![]() In other words, points
In other words, points ![]() and
and ![]() of the Twisted Edward curve cannot be attained by the map defined by this substitution. Note also that the change of variable dictates that
of the Twisted Edward curve cannot be attained by the map defined by this substitution. Note also that the change of variable dictates that
![]()
- Case
 Since
Since  the Montgomery form dictates that
the Montgomery form dictates that  As a result the point
As a result the point  of the Montgomery curve must be excluded.
of the Montgomery curve must be excluded. - Case
 The Montgomery form dictates that
The Montgomery form dictates that  And so
And so  or
or  Since we assumed that
Since we assumed that  is a quadratic non-residue, the discrimant of
is a quadratic non-residue, the discrimant of  cannot be a square. Hence, this quadratic has no roots over
cannot be a square. Hence, this quadratic has no roots over 
Consequently, the only two points of the Montgomery curve that are not covered by this substitution are the point at infinity ![]() and the point
and the point ![]() We will deal with them separately. After applying the change of variable, we get
We will deal with them separately. After applying the change of variable, we get
![]()
After simplication, we obtain
![]()
Since ![]() and
and ![]() we simplify further and obtain
we simplify further and obtain
![]()
We recognize this as a Twisted Edward form with ![]() and
and ![]() This is a valid representation because
This is a valid representation because
 (since
(since  for a Montgomery curve)
for a Montgomery curve)
We then get the following inverse transformation:
![]()
![]() , if
, if ![]()
![]()
![]()
The maps ![]() and
and ![]() demonstrate the existence of a birational equivalence between the following two sets:
demonstrate the existence of a birational equivalence between the following two sets:
- Twisted Edward curves with
 a quadratic residue and
a quadratic residue and  a quadratic non-residue over
a quadratic non-residue over 
- Montgomery curves with
 (
( ) a quadratic residue and (
) a quadratic residue and ( ) a quadratic non-residue over
) a quadratic non-residue over  .
.
Finally, note that one could transform such a Twisted Edward curve into a short form Weierstrass curve by applying the composition map ![]() Readers interested in learning more about Twisted Edward curves can consult [2].
Readers interested in learning more about Twisted Edward curves can consult [2].
Monero’s curve: The elliptic curve cryptography used by Monero [8] relies on a particular Twisted Edward curve known as ![]() [3]. It has the following attributes:
[3]. It has the following attributes:
 is the prime number given by
is the prime number given by  explaining the suffix in the curve’s name. It defines the underlying finite field
explaining the suffix in the curve’s name. It defines the underlying finite field  In hex notation using 256 bit-long representation, it is given by
In hex notation using 256 bit-long representation, it is given by
 7FFFFFFF FFFFFFFF FFFFFFFF FFFFFFFF FFFFFFFF FFFFFFFF FFFFFFFF FFFFFFED
7FFFFFFF FFFFFFFF FFFFFFFF FFFFFFFF FFFFFFFF FFFFFFFF FFFFFFFF FFFFFFED In standard hex notation, it is given by
In standard hex notation, it is given by
 7FFFFFFF FFFFFFFF FFFFFFFF FFFFFFFF FFFFFFFF FFFFFFFF FFFFFFFF FFFFFFEC
7FFFFFFF FFFFFFFF FFFFFFFF FFFFFFFF FFFFFFFF FFFFFFFF FFFFFFFF FFFFFFEC . In standard hex notation, it is given by
. In standard hex notation, it is given by
 52036CEE 2B6FFE73 8CC74079 7779E898 00700A4D 4141D8AB 75EB4DCA 135978A3
52036CEE 2B6FFE73 8CC74079 7779E898 00700A4D 4141D8AB 75EB4DCA 135978A3Since
 and
and  this curve qualifies as a Twisted Edward curve. Moreover,
this curve qualifies as a Twisted Edward curve. Moreover,  is a quadratic residue over
is a quadratic residue over  while
while  is not. Consequently, this curve admits a birationally equivalent Montgomery form known as Curve25519. The underlying set of the group associated with this Twisted Edward curve is given by
is not. Consequently, this curve admits a birationally equivalent Montgomery form known as Curve25519. The underlying set of the group associated with this Twisted Edward curve is given by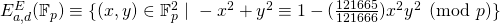
Here is a euclidean representation of this curve when
 (it is not feasible to show it for the value of
(it is not feasible to show it for the value of  )
)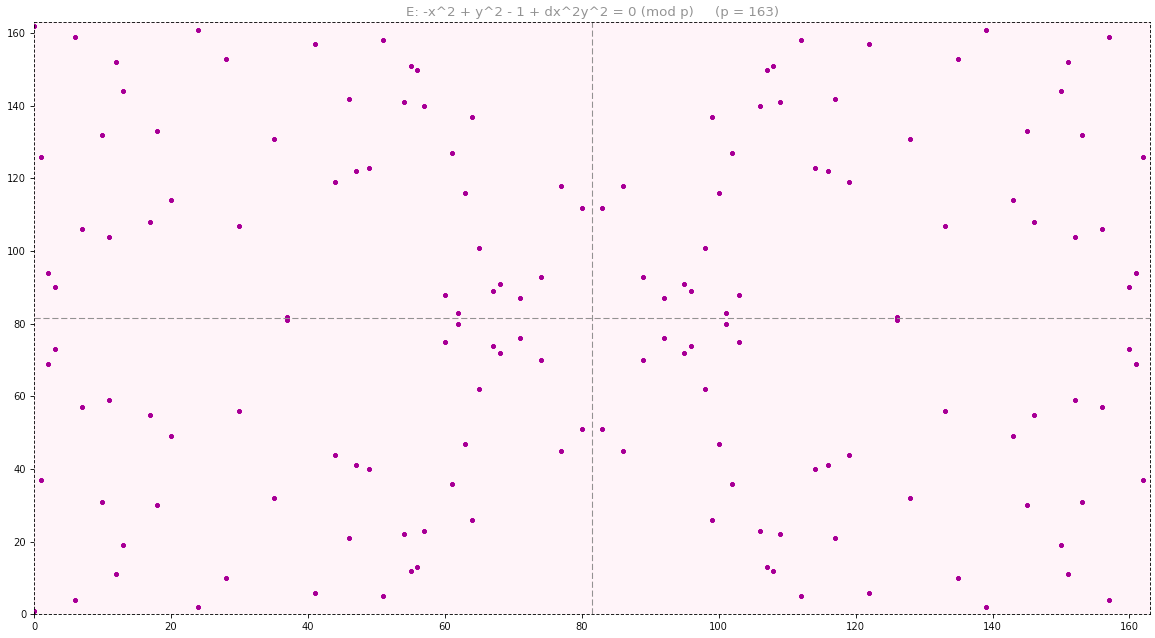
- The base point
 has abscissa and ordinate given by
has abscissa and ordinate given by





which in standard hex notation are given by:
 216936D3 CD6E53FE C0A4E231 FDD6DC5C 692CC760 9525A7B2 C9562D60 8F25D51A
216936D3 CD6E53FE C0A4E231 FDD6DC5C 692CC760 9525A7B2 C9562D60 8F25D51A 66666666 66666666 66666666 66666666 66666666 66666666 66666666 66666658
66666666 66666666 66666666 66666666 66666666 66666666 66666666 66666658Monero’s public-key cryptography is hence conducted on the subgroup whose underlying set is

- The order of
 is chosen to be a prime number equal to
is chosen to be a prime number equal to
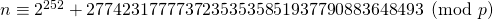
Which in standard hex notation is given by
 10000000 00000000 00000000 00000000 14DEF9DE A2F79CD6 5812631A 5CF5D3ED
10000000 00000000 00000000 00000000 14DEF9DE A2F79CD6 5812631A 5CF5D3ED - Recall that
 denotes the order of
denotes the order of  , and must divide
, and must divide  i.e., the order of
i.e., the order of  The cofactor
The cofactor  is equal to
is equal to  which in this case evaluates to 8. It is represented in standard hex notation by
which in this case evaluates to 8. It is represented in standard hex notation by
 00000000 00000000 00000000 00000000 00000000 00000000 00000000 00000008
00000000 00000000 00000000 00000000 00000000 00000000 00000000 00000008
References
[1] behindtext. why did bitcoin choose secp256k1 over secp256r1?
[2] D. J. Bernstein, Peter Birkner, Marc Joye, Tanja Lange, and Christiane Peters. Twisted edwards curves. AFRICACRYPT, pages 389-405, 2008.
[3] Daniel J. Bernstein, Niels Duif, Tanja Lange, Peter Schwabe, and Bo Yin Yang. High-speed high-security signatures. Cryptographic Hardware and Embedded Systems, pages 124-142, 2011.
[4] Anne-Sophie Charest. Pollard’s p-1 and lenstra’s factoring algorithms.
[5] Hal Finney. secp256k1.
[6] ImperialViolet. What a difference a prime makes, December 2010.
[7] Certicom Research. Sec 2: Recommended elliptic curve domain parameters. Standards for Efficient Cryptography, 2010.
[8] N. Van Saberhagen. Cryptonote 2.0. , 2013.
[9] R. Schoof. Elliptic curves over finite fields and the computation of square roots mod p. Mathematics of computation, 44(170):483-494, 1985.
[10] J. Silverman. The Arithmetic of Elliptic Curves. Springer, second edition, 2009.
[11] Nick Sullivan. How the nsa (may have) put a backdoor in rsa’s cryptography: A technical primer , January 2014.
Tags: Curve25519, ed25519, Edward, elliptic curve, elliptic curve group, Montgomery, Twisted edward, Weierstrass

No comments
Comments feed for this article
Trackback link: https://delfr.com/elliptic-curve-cryptography/trackback/